The Dark Web is a place full of underground criminals and intelligent hackers, but it is also a place much more secure than your favorite browser. It’s hardly a secret that when you go online, your activities are followed, not only by Google, Facebook, and Amazon but also by official surveillance teams and hackers.
We often recommend privacy add-ons and software that block at least some web trackers, but if you really want to preserve your anonymity, the Dark Web browser named Tor is the best option available. Tor will be used in this blog to discuss the do’s and don’ts when using the Dark Web.
What Does Tor Do?
Tor keeps your web activities safe from spammers and advertisers, hides your data from corporations and other web users, and lets you browse without being followed by identity thieves and stalkers.
What Can You Do with Tor?
You can send personal photos without having them intercepted, use social networks without being monitored, write genuinely anonymous blog posts, and much more. For access information, check out How to get dark web access.
Top Five Safe Ways to Use a Dark Website
Do #1: Ensure Tor is Always Updated
Tor is much more secure than Chrome and Firefox, but as with any software, it’s not impervious to attack. For example, the network was targeted in 2013 by a Trojan called Chewbacca, who stole banking details.
In 2016, it was revealed that the FBI had used specially created malware called Torsploit to ‘deanonymize’ Tor users and track their real IP addresses. There have also been cases of Tor exit nodes (the last relays that Tor traffic passes through before it reaches its destination) being used for malicious purposes rather than anonymous ones, and infecting users’ systems.
Fortunately, Tor usually addresses such threats and vulnerabilities very swiftly, making it essential to keep the browser up to date.
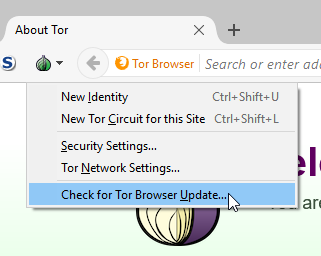
- Every time you launch Tor, click the onion icon on the toolbar and choose ‘Check for Tor Browser Update’ (Tor updates itself periodically, but manually updating it ensures you’re using the latest version).
- Additionally, if you’re using a service that involves sharing personal information, you should change Tor’s security level to High.
Don’t #1: Use Tor for Torrenting
As a powerful privacy tool, Tor might seem like the perfect means of downloading and uploading files via BitTorrent and other peer-to-peer networks, but it is not! Using a torrent client bypasses Tor’s protection and blows your anonymity by sending your real IP address to the torrent service and other ‘peers.’ This action allows them to identify you, the port you’re using for torrenting, and even the data you’re sharing, if it isn’t encrypted.
They can then potentially target you with malware or even notify the relevant authorities (if you’re sharing copyrighted material). Additionally, torrent traffic places a massive strain on the Tor network and slows it down for others, so it’s selfish and careless.
For all these reasons, Tor says file-sharing is “widely unwanted,” and exit nodes are configured by default to block torrent traffic.
Do #2: Create a new identity when necessary
Tor does a great job of keeping you safe and anonymous, but you may still encounter websites that raise alarm bells. Tor may warn you that a site is trying to track you.
If you’re worried that your privacy has been compromised, do the following:
- Click the onion icon on the toolbar.
- Choose “New Identity.” This option will restart the Tor browser and reset your IP address, so you can carry on browsing as a fresh user.
Don’t #2: Maximize the Tor Window
Leave Tor browser windows at their default size because maximizing them allows websites to determine the size of your monitor. This suggestion may not seem significant on its own, but combined with other data, it may provide the “extra” information websites need to identify you.
Do #3: Use a VPN Alongside Tor
It’s important to remember that Tor is a proxy rather than a VPN, which only protects traffic routed through the Tor browser. As we explained earlier, there are some risks to using the Tor network, especially when downloading torrent files and inadvertently connecting through a malicious exit node.
You can boost your privacy and security by using Tor in conjunction with a VPN, to ensure all your data is encrypted and no logs are kept for your activities. Several VPNs offer features explicitly designed for Tor users, including:
- ProtonVPN, which lets you access servers pre-configured to redirect traffic through the Tor network
- ExpressVPN, which enables you to sign up anonymously through its ‘.onion’ website
- AirVPN, which routes traffic through the Tor network first and then through the VPN
None of the above VPN options are free, but they are faster, more flexible, and more trustworthy than free VPN services.
Don’t #3: Search The Web Using Google
Google isn’t known for respecting its users’ privacy, so to continue using it in Tor (it’s one of the available options) is rather self-defeating.
Not only does Google still try to track you and record your searches (based on your exit node’s IP address), but it also gets very snobbish and arrogant when it finds you’re connecting in an ‘unusual’ manner. Try searching with Google in Tor, and you’ll continually get CAPTCHAs that ask you to prove you’re not a robot.
We recommend using Tor’s default privacy search engine DuckDuckGo, its ‘Onion’ variant, or Startpage (which uses non-tracked Google results), all of which come pre-installed alongside Google.

Do #4: Consider Running a Tor Relay
Tor relies on its loyal and ever-expanding community to provide relays that create circuits and deliver anonymity. The more relays or ‘nodes’ that are currently running, the faster and more secure the Tor network will be.
If you become a regular Tor user, consider giving back to the community by sharing your bandwidth and running your relay. You can either be a ‘middle relay,’ which is one of the two or more nodes that receive Tor traffic and then passes it on, or an ‘exit relay.’
Being a middle relay is much safer. If another user employs the Tor network to do something malicious or illegal, your IP address will not show up as the source of the traffic.
In contrast, an exit relay can be identified as that source, which means people who run exit relays may have to deal with complaints and even legal attention. Therefore you shouldn’t host an exit node from your home PC and, if you’re sensible, not at all!
One further problem: you need to have a Linux computer running Debian or Ubuntu to host a reliable relay. In Windows, you need to run a Linux distro as a virtual machine to set up your relay. It’s a bit of a hassle, but at least it will keep your Tor traffic separate from the rest of your system.
Don’t #4: Share Your Real Email Address
There’s no point in using Tor to stay anonymous if you sign up to a website using your real email address. It’s like putting a paper bag over your head, and writing your name and address on it. A disposable email service such as MailDrop or the brilliant Fake Name Generator can create a temporary address and identity for site registrations and keep your Tor persona separate from your standard web one.

Do #5: Use Tor for Anonymous Email
You can use your favorite email services in Tor, although Google may ask you to verify your Gmail account. However, the content of your messages won’t be encrypted in transit. Tor will, of course, disguise where you are, but unless you’re using a disposable email address (see above), anyone intercepting your messages will see your real email address and, potentially, your name.
For total privacy and anonymity, you can use a Tor-enabled email service. Several of these have been closed down by law-enforcement agencies in recent years because they were linked to criminal activities, but using one is not illegal, nor does it place you under suspicion. The best and most trustworthy option is ProtonMail, an end-to-end encrypted email provider, launched by the CERN research facility in 2013.
Earlier this year, ProtonMail introduced a Tor hidden service specifically to combat the censorship and surveillance of its users. You can sign up for a free ProtonMail account at protonirockerxow.onion, but this limits you to 500MB of storage and 150 messages per day; to get advanced features, you need the Plus plan ($5.00 per month).
Because Tor is based on Firefox, it is still possible to install your favorite add-ons to suit your preferences, which makes sense if you are planning to use Tor as your default browser. Don’t be tempted! Even if extensions aren’t infected with malware (as some Chrome ones were recently found to be), they may seriously compromise your privacy.
Tor comes with two of the best protective add-ons preinstalled – NoScript and HTTPS Everywhere – and that’s really all you need if your reason for switching to the browser is to be anonymous. Also, bear in mind that browsing with Tor can be slower than Chrome or Firefox because of its roundabout way of connecting, so overloading it with add-ons will further reduce your speed.
Alternatively, you could try Bitmessage, a free Desktop client that lets you send and receive encrypted messages using Tor, and can be run from a USB stick.
Don’t #5: Go Overboard with Browser Add-Ons
Because Tor is based on Firefox, it is still possible to install your favorite add-ons to suit your preferences, which is understandable if you are planning to use Tor as your default browser. Don’t be tempted! Even if extensions aren’t infected with malware (as some Chrome ones were recently found to be), they may seriously compromise your privacy.
Tor comes with two of the best protective add-ons preinstalled – NoScript and HTTPS Everywhere – and that’s all you need if your reason for switching to the browser is to be anonymous. Also, bear in mind that browsing with Tor can be slower than Chrome or Firefox because of its roundabout way of connecting, so overloading it with add-ons will further reduce your speed.
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.


