If you want to know how to access the dark web, you’ll first want to know the differences between the dark web and the deep web, and whether or not the dark web is a safe place to be.
To bring you up to speed, the deep web is the vast, subsurface portion of the internet encompassing everything that’s not crawled by conventional search engines. The dark web is a purposefully obfuscated subsection of this, linked to shady activity but also a useful platform for privacy activists living under oppressive regimes. Here’s how to get to it.
How to access the dark web
What is the dark web?
Created in the mid-1990s by military researchers in the US, the technology which paved the way for what is now known as the dark web was used by intelligence officers to share files anonymously. That initial platform was called ‘Tor’, which stands for ‘The Onion Router’.
They rolled it out to the public to make it harder for outsiders to distinguish what was a government file and what was simply data being sent by an everyday citizen. In summary, the more people using it, the more “noise” there is, disguising the government message trail.
Tor is a critical part of the dark web and hosts around 30,000 of the network’s hidden sites.
To access the dark web, you’ll need an anonymized proxy network. The two most popular tools in this particular toolbox are Tor and I2P. You can find a thorough breakdown of the differences between the two networks here, but for the purpose of this guide, we’ll go with Tor as it’s the most widely used.
What is Tor?
Tor is an anonymity network that hides your identity as you browse the web, share content, and engage in other online activities. It encrypts any data sent from your computer so that no one can see who or where you are, even when you’re logged into a website. Tor is an acronym for The Onion Router, and it was created by the US Naval Research Laboratory in the mid-Nineties.
The most recent figures (metrics.torproject.org) suggest Tor has around 2.5 million daily users, with Facebook’s Tor-only website alone attracting more than a million visitors every month.
What’s it got to do with onions?
It’s all about layers. The data from your computer is sent through a series of ‘nodes’ (other computers, also known as ‘relays’) run by millions of volunteers around the world, building up layers of encryption like the layers of an onion. Tor gives you a different IP address every time you send or request data, disguising your real one and making it nearly impossible for prying eyes to know where the data originated.
How do I use Tor?
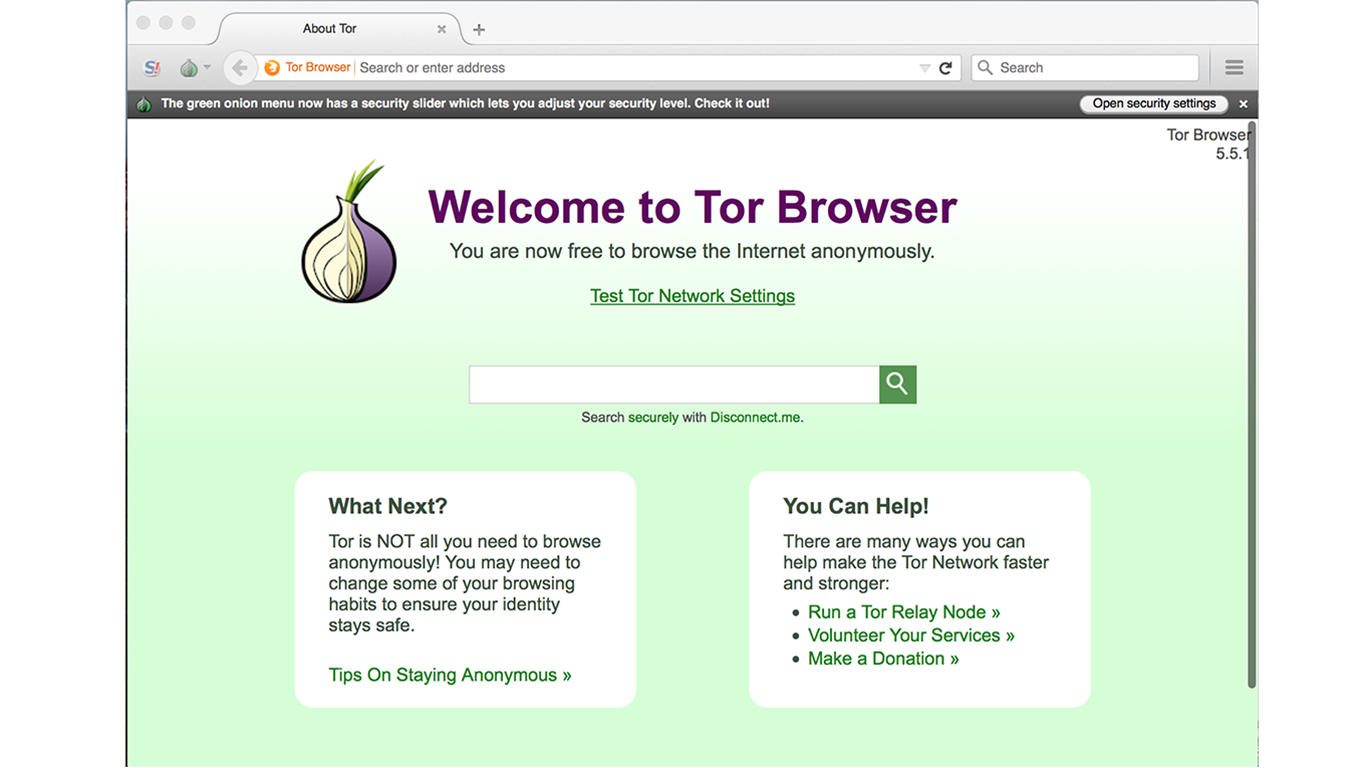
The easiest way to use Tor is through its dedicated browser, which is available for Windows, MacOS, and Linux (it can be run from a USB stick if you don’t want to install it on your computer). The Tor browser is based on Firefox but disables plugins that could compromise your privacy and security.
It won’t clash with other software you have installed, but you may need to configure your antivirus program or firewall to allow it access to the internet.
There’s also a Tor app for Android, called Orbot; and an operating system – Tails – that’s preconfigured to use Tor.

You can also download everything you need to get started with Tor on the Tor Project website. Simply click Download Tor and follow the instructions.
How to connect or configure Tor
Download TOR from the official website from any web browser.

The first time you use Tor you’ll be faced with a pop-up asking you to connect or configure the Tor network.
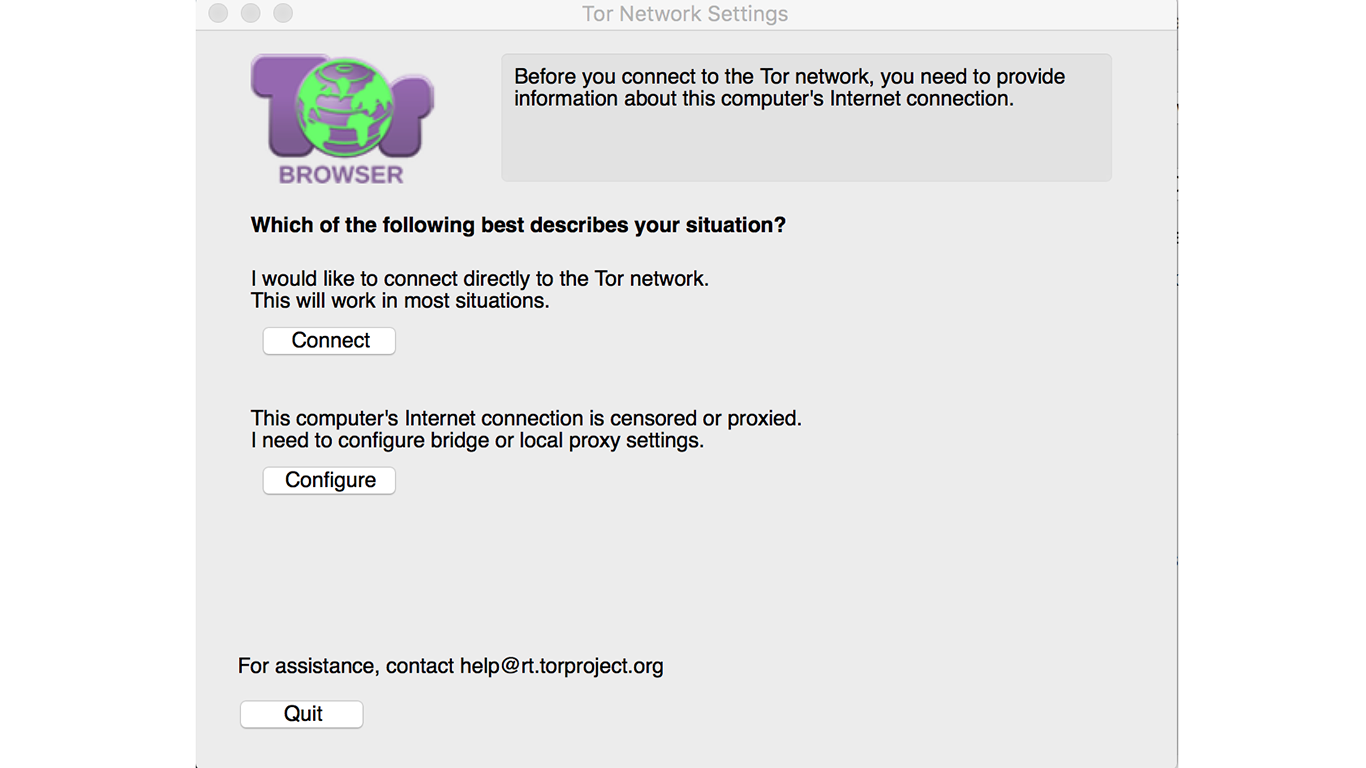
The majority of people will be able to click Connect, but if you’re on a censored or proxied internet connection you’ll need to configure your local proxy settings. If that’s something you need to do, the Tor Project has plenty of manuals on the nitty-gritty of configurations.
How to use Tor to get somewhere
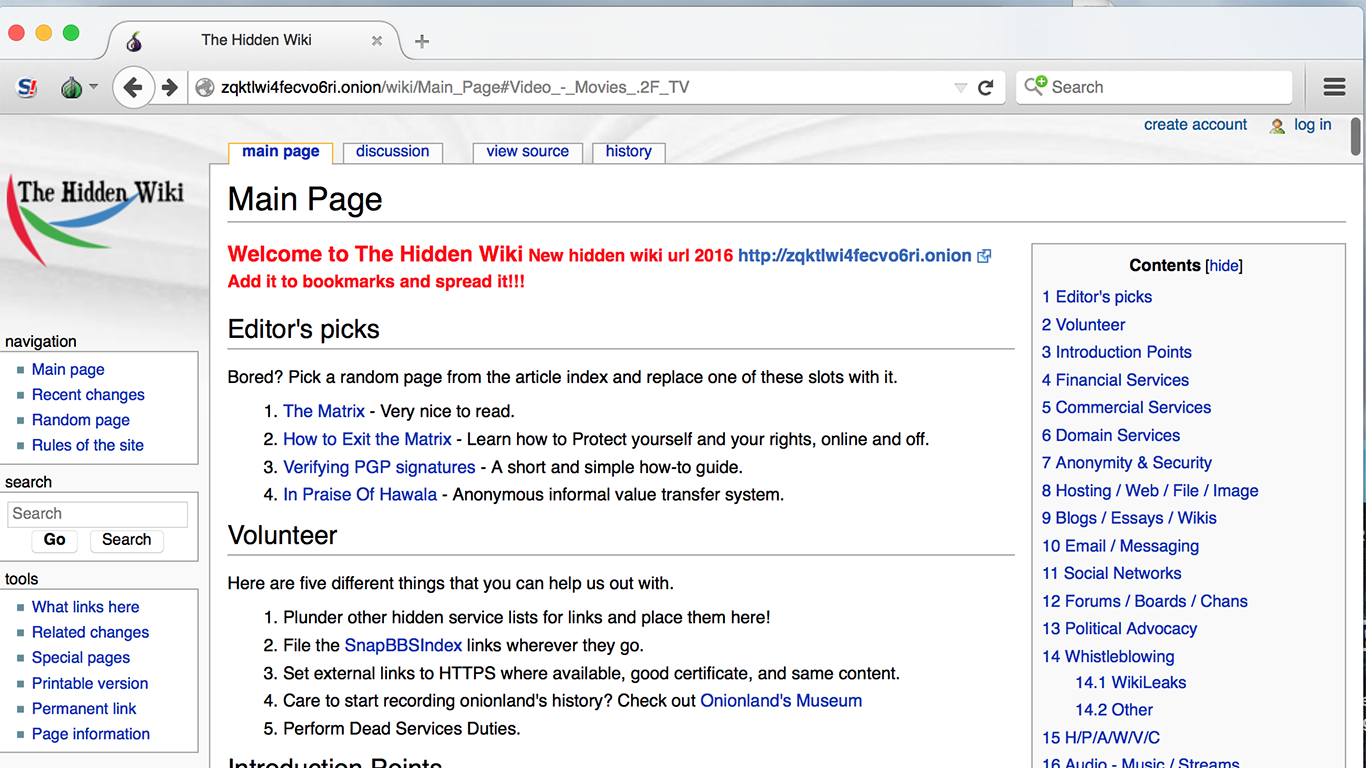
The Tor window will look like a normal browser window, but you can now use it to access sites with a .onion suffix. Coming across these sites isn’t a matter of searching Google – you’ll need to find specific links.
What’s more, the addresses of these links tend to be a cluster of seemingly random letters, so it isn’t always entirely clear where they’re leading you.
The Hidden Wiki is one of the better-known resources for traversing the dark web, where you’ll find links to sites across various categories. Another useful resource is the subreddit r/onions. Obviously, be aware that both of these contain NSFW material.
If you’re particularly keen on maintaining anonymity, The Tor Project includes a number of warnings about what not to do when browsing the dark web. We would advise you to be extremely careful when using Tor. If you’re worried about privacy and online tracking, there are easier ways to take steps to protect your data. From anonymous search engines such as DuckDuckGo and Oscobo to plugins such as Ghostery, there are simple ways to block trackers used by ad networks.
Who uses Tor?
The police, the military, medical researchers, human-rights groups, abuse victims, whistleblowers, journalists, and, increasingly, anyone else who wants to keep their online activities private or is concerned about cyber-spying. It is very popular among people in internet-censored countries such as Russia and the UAE and counts Human Rights Watch among its past donors.
NSA whistleblower Edward Snowden is a big fan and says: “Without Tor, the streets of the internet become like the streets of a very heavily surveilled city. With Tor, we have private spaces and private lives, where we can choose who we want to associate with and how”.
But isn’t Tor a bit dodgy?
Every medium, from the printed page to a standard browser, has the potential to be dodgy, but web services do not commit ‘actions’ – their users do. As with technology such as Bitcoin – Tor’s preferred currency – Tor does not incite or condone illegal enterprises. On its website, it recognizes that criminal elements exploit anonymity, but points out: “Criminals can already do bad things… they already have lots of options available”.
For every lawbreaker, there are numerous legitimate users, many of whom use Tor to great social benefit.
So Tor is completely legal?
Yes, completely. The US Navy isn’t in the habit of creating illegal software, and there’s nothing dubious about wanting to browse in private. Nobody has ever been arrested or prosecuted solely for using Tor, only for what they used it to do, and Tor itself says in its legal FAQ that “it is not a tool designed or intended to be used to break the law.”
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.


