A network administrator used to be a job for IT specialists in big companies. However, the world has grown more technologically advanced, so now, small and large businesses, households, and libraries have their own network to manage and maintain. These days, setting up a Wi-Fi connection is easy and inexpensive.
Some users have a Wi-Fi network running off their cable or DSL internet service, while others run Wi-Fi using their smartphone as an access point. Most smartphones have the capacity to act as a mobile hot spot. In any case, there is always the risk of unauthorized access to your Wi-Fi network and router.
This article explains various methods to discover if someone is using your Wi-Fi without permission, as well as summarized ways to secure your Wi-Fi from potential intruders.
Signs That Someone is Accessing Your Wi-Fi
Regardless of how many people use Wi-Fi now, most haven’t been trained or educated in network security. That means your Wi-Fi network may well be vulnerable to malicious hackers or those who simply want to use your Internet access for free; either way, it’s unwanted and unlawful.

You should be aware of certain warning signs that indicate that someone is connected to your network without permission. One common sign is slower Internet speed. Every Internet connection takes up some bandwidth, and if someone is downloading torrents or playing online games on your network without your permission, then your traffic slows down.
Knowing who is using your Wi-Fi and when is crucial for keeping your network secure. This tutorial explains how to check if someone is using your Wi-Fi, how to kick them off, and how to help prevent them and anyone else from accessing your Wi-Fi again.
How to Check Who is Using Your Wi-Fi Network
There are several ways to detect whether or not someone is using your wireless network, such as obtaining direct router access via a browser or using router checker apps.
Turn Off All Devices to Check if Someone’s Accessing Your Wi-Fi
One low-tech way is to shut off all your computers, smartphones, and tablets so that none of your devices are turned on. Then, check the activity lights on your wireless router (often called a wireless modem if you’re connected to cable or DSL broadband Internet). If regular activity still appears on the router even though none of the authorized users are powered on, then that’s usually a sign that someone is using your Wi-Fi without your permission. The term “usually” is used because your router may also undergo occasional configuration processes or receive updates, or it may ping stored devices to check for connectivity, whether they are on or off.
Use a Web Browser to Access Your Router to Check for Unidentified Devices
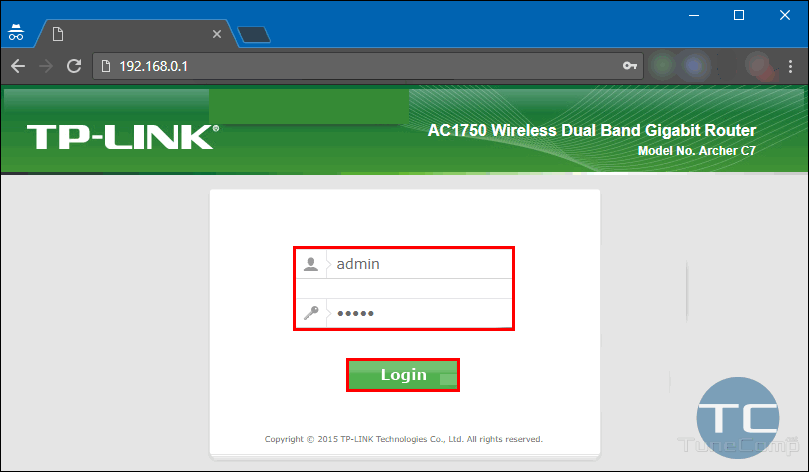
The next step is to use a web browser to log onto your wireless router’s access page. Nearly all home routers have an online access page that you can get to from any computer that is linked to the router. Here are the most common procedures based on brand.
Common URLS for Routers
The URL to type into your browser window varies from router to router, but it’s almost always an IP address. You can find the exact URL by checking your router documentation. The information is also usually found on the back of the router. Check to see if the address is printed on the label, or by using the default addresses: a huge number of routers use http://192.168.0.1 or http://192.168.1.1.
- If you use Xfinity (Comcast) to access the Internet, the default URL for accessing your router/modem is most likely http://10.0.0.1/.
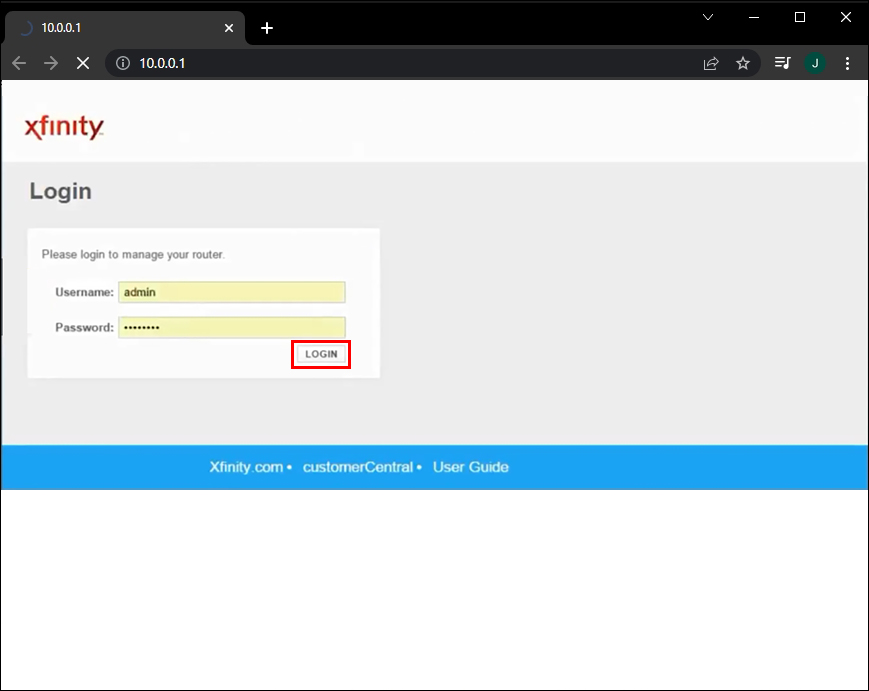
- You can just enter the number (e.g., “192.168.0.1”) in the address bar of your browser and hit enter. This will take you to the administrative interface for your router. You can find details on Netgear router setup procedures, Belkin router setup help, and information on Asus router setup processes.
Default Router Login Credentials
You’ll need to know the administrator password for your router to log in. Of course, you should change it from the default password to one you can remember, but don’t make it too easy! Regardless, you should have recorded the default or the new password when you set up your router, or after it was set for you by an installation technician.
- The most common default username is “admin,” and the most common default password is usually “wireless” or “admin” as well. Another very common default password is “1234.”
- If you use a router/modem provided with your Comcast/Xfinity service and haven’t changed the password from the original one, the default username may be “admin” and the default password is probably “password.”

Identifying Connected Devices
- Once you’ve successfully logged on to your router, navigate to the administration page to view the list of connected devices. On a Netgear router, this is usually listed under “Maintenance > Attached Devices.” On a Linksys router, it’s typically found under “Network Map” or “Device List.”

- Other routers have their own organizational structure for this information, but every router should provide it.
- Other routers have their own organizational structure for this information, but every router should provide it.
- Once you are on the list, you can identify every device based on its MAC address.
All you need to know for now is that every device has its own unique number that’s used to identify it on the Local Area Network (LAN), which is your Wi-Fi network in this case, making it a Wireless Local Area Network (WLAN).
You can find the MAC address for all your computers, compare them to the list, and then see if there are any devices on the list that you don’t recognize. Most Wi-Fi devices have an option in the settings menu that displays the MAC address, such as Android smartphones and tablets, laptops, Roku devices, Fire TV Sticks, Smart TVs, etc.
If you have trouble identifying all the devices listed, turn all devices off or refresh the map. It’s a process of elimination. Don’t forget to include Google or Alexa controlled devices and any other equipment connected to your WLAN.
If all this messing around with MAC address and router management pages is a bit outside of your technical comfort zone, don’t worry. There are some excellent third-party tools that will help you do the job.
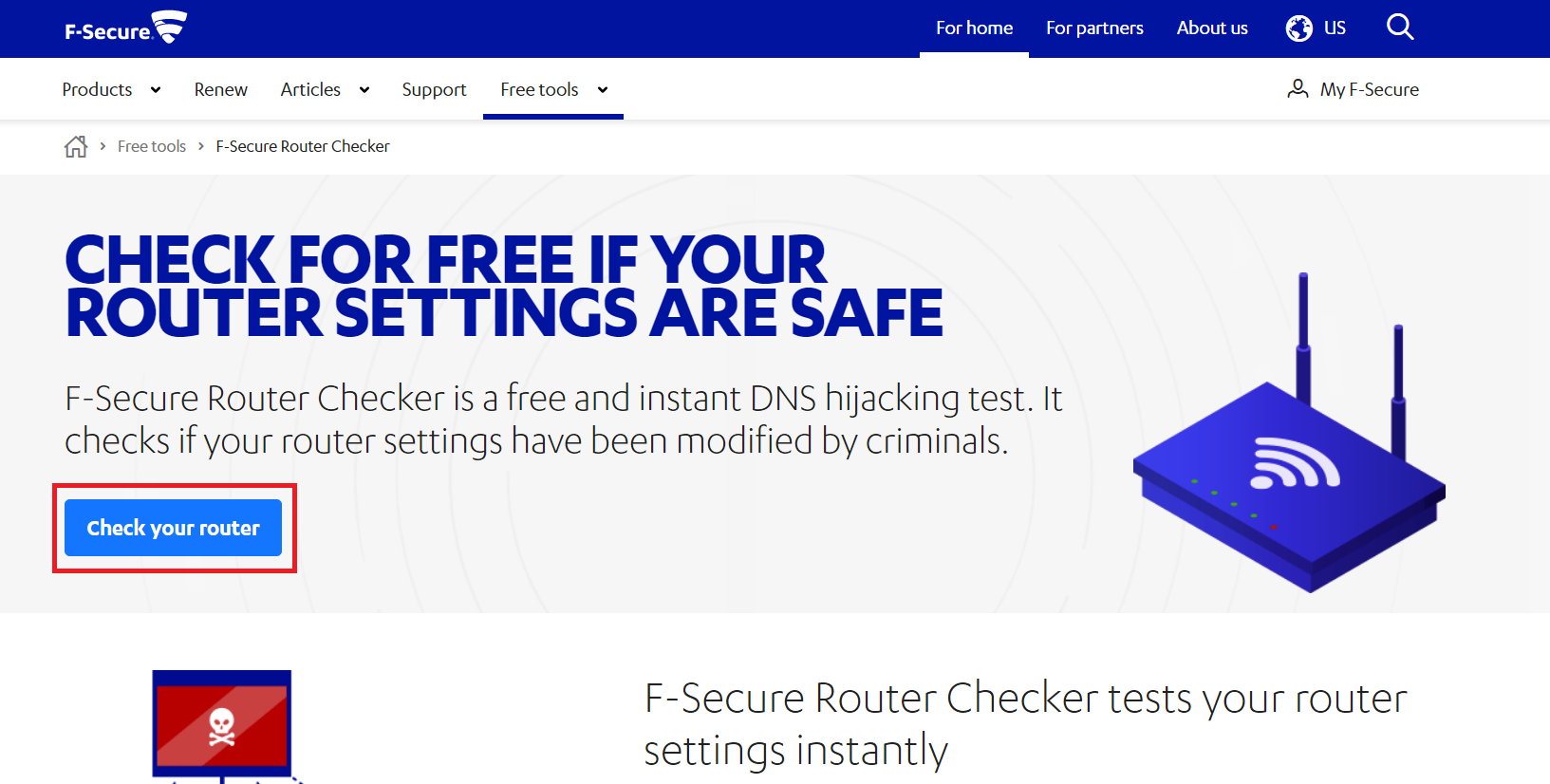
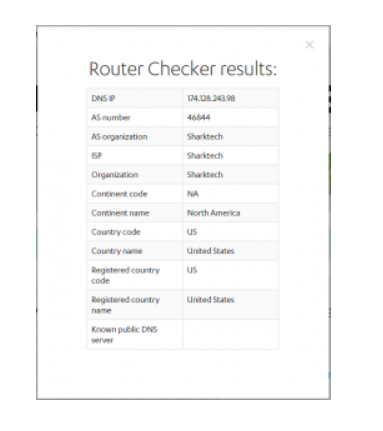
Use F-Secure Router Checker
One such great tool is the F-Secure Router Checker. It is a free and quick solution to see whether your router had been hijacked or not.
- Just navigate to the website, select the blue “Check Your Router” button and let the website do its work.

- It will assess any vulnerabilities in your router and alert you to them.

Use Wi-Fi Monitor on Android

Another route is to download Wi-Fi Monitor, a Google Play app that scans your Wi-Fi network and tells you what devices use it. It is an excellent way to identify devices accessing your network.
How to Secure Your Wi-Fi Network from Intruders
What should you do if you identify someone using your Wi-Fi network without your permission? The first step is to remove them and then make sure they won’t be able to do it again.
Change Your Wi-Fi Password
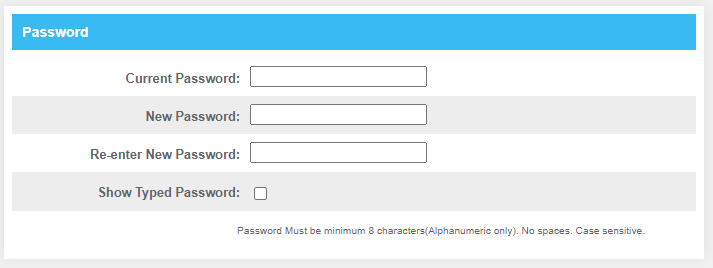
The instructions below are tested using a Linksys Smart Router. Your router may differ slightly and use different terminology. Just adapt the following instructions to your specific model.
- Log into your router and access the admin interface.

- Select the Wireless part of the interface.

- Turn off your wireless network. On a Linksys router, this is a toggle. This will kick everyone off your
Wi-Fi, so notify anyone beforehand.
- Select “WPA2” as the wireless security mode if it isn’t already selected. This is the best option for most users.

- Change the wireless access password and save changes.

- Enable wireless once more.

If your router doesn’t support WPA2, you should upgrade; it’s the de facto standard for wireless security.
Change the password to something that is as difficult as it is practical while still being able to remember it. Mix upper- and lower-case letters and numbers. If your router allows special characters, use them for good measure.
Extra steps you can take to secure your Wi-Fi from intruders includes disabling Wi-Fi protected setup (WPS) and upgrading the router firmware.
Disable Wi-Fi Protected Setup (WPS) to Enhance WLAN Security
There should be a setting in the wireless part of your router that disables WPS. This is a known vulnerability in shared properties, dorms, and other places where you don’t control who comes and goes. Turn it off to stop people from authenticating on your network if they have physical access to the router hardware.
Upgrade Router Firmware to Enhance WLAN Security
Upgrading router firmware allows you to benefit from any security patches or fixes. The KRACK vulnerability is one example that found a weakness in WPA2 which was quickly patched out. Only a router firmware update can fully protect you, so allow automatic updates on your router if it is possible or check regularly for updates. Often times you have to download the firmware update directly from the router manufacturer’s website because many ISPs block such updates.

Keeping Tabs on Your Wi-Fi
In closing, the above recommendations help secure your WLAN and Wi-Fi router to prevent unauthorized users, as well as hackers. If you want to take your privacy one step further, check out how to secure your PC. Share your experiences in the comments below.
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.