For many IT experts, Wireshark is the go-to tool for network packet analysis. The open-source software enables you to closely examine the gathered data and determine the root of the problem with improved accuracy. Furthermore, Wireshark operates in real-time and uses color-coding to display the captured packets, among other nifty mechanisms.
In this tutorial, we’ll explain how to capture, read, and filter packets using Wireshark. Below, you’ll find step-by-step instructions and breakdowns of the basic network analysis functions. Once you master these fundamental steps, you’ll be able to inspect the traffic flow of your network and troubleshoot problems with more efficiency.
Analyzing Packets
Once the packets are captured, Wireshark organizes them in a detailed packet list pane that’s incredibly easy to read. If you want to access the information regarding a single packet, all you have to do is locate it on the list and click. You can also further expand the tree to access the details of each protocol contained within the packet.
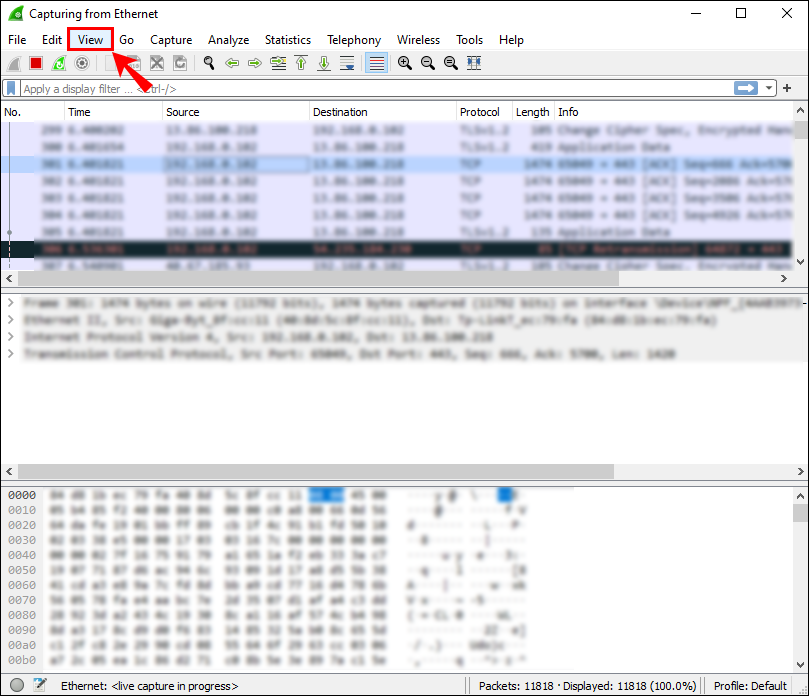
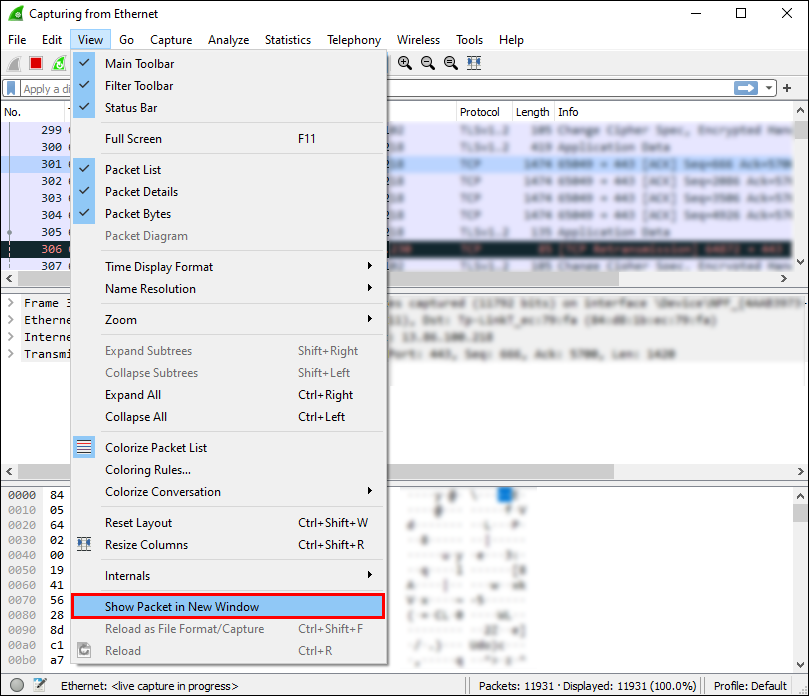
For a more comprehensive overview, you can display each captured packet in a separate window. Here’s how:
- Select the packet from the list with your cursor, then right-click.

- Open the “View” tab from the toolbar above.

- Select “Show Packet in New Window” from the drop-down menu.

Note: It’s much easier to compare the captured packets if you bring them up in separate windows.
As mentioned, Wireshark uses a color-coding system for data visualization. Each packet is marked with a different color that represents different types of traffic. For example, TCP traffic is usually highlighted with blue, while black is used to indicate packets containing errors.
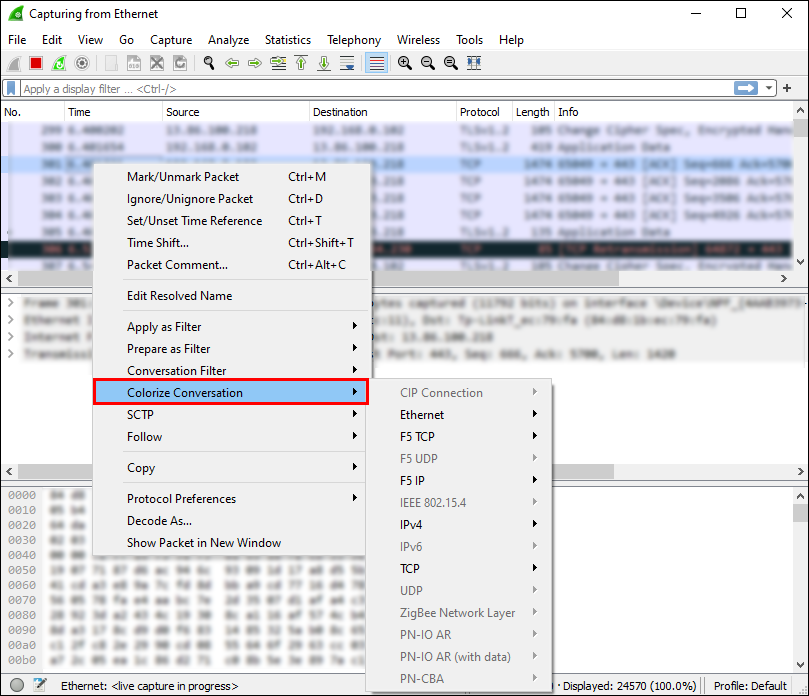
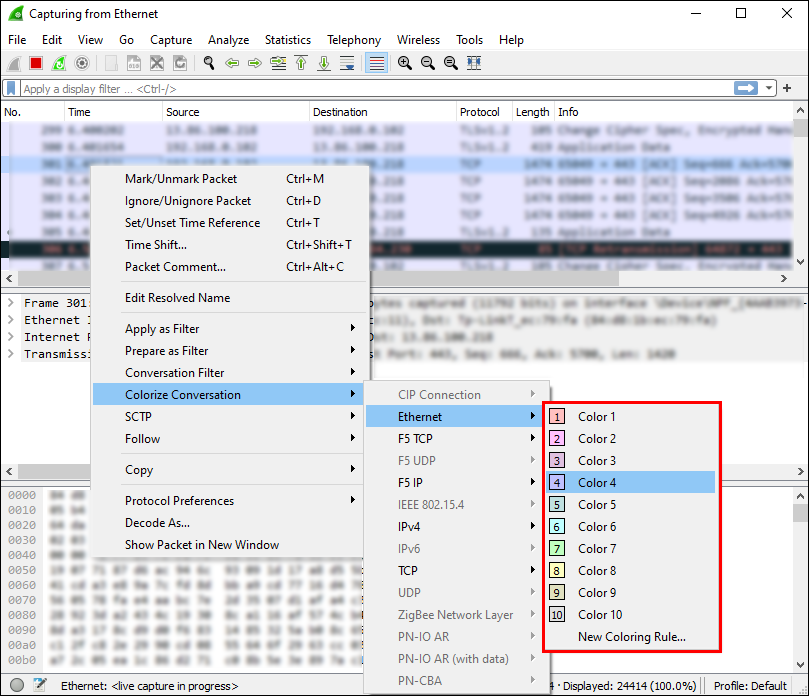
Of course, you don’t have to memorize the meaning behind each color. Instead, you can check on the spot:
- Right-click on the packet you wish to examine.

- Select the “View” tab from the toolbar at the top of the screen.

- Choose “Coloring Rules” from the drop-down panel.

You’ll see the option to customize the colorization to your liking. However, if you only want to change the coloring rules temporarily, follow these steps:
- Right-click on the packet in the packet list pane.
- From the list of options, select “Colorize With Filter.”

- Choose the color with which you want to label it.

Number
The packet list pane will show you the exact number of captured data bits. Since the packets are organized in several columns, it’s fairly easy to interpret. The default categories are:
- No. (Number): As mentioned, you can find the exact number of captured packets in this column. The digits will remain the same even after filtrating the data.
- Time: As you might’ve guessed, the packet’s timestamp is displayed here.
- Source: It shows where the packet originated.
- Destination: It shows the place where the packet will be kept.
- Protocol: It displays the name of the protocol, typically in an abbreviation.
- Length: It shows the number of bytes contained in the captured packet.
- Info: The column includes any additional information about a particular packet.
Time
As Wireshark analyzes the network traffic, each captured package is time stamped. The timestamps are then included in the packet list pane and available for later inspection.
Wireshark doesn’t create the timestamps themselves. Instead, the analyzer tool gets them from the Npcap library. However, the source of the timestamp is actually the kernel. That’s why the accuracy of the timestamp can vary from file to file.
You can choose the format in which the timestamps will be displayed in the packet list. In addition, you can set the preferred precision or number of decimal places that are displayed. Apart from the default precision setting, there’s also:
- Seconds
- Tenths of a second
- Hundredths of a second
- Milliseconds
- Microseconds
- Nanoseconds
Source
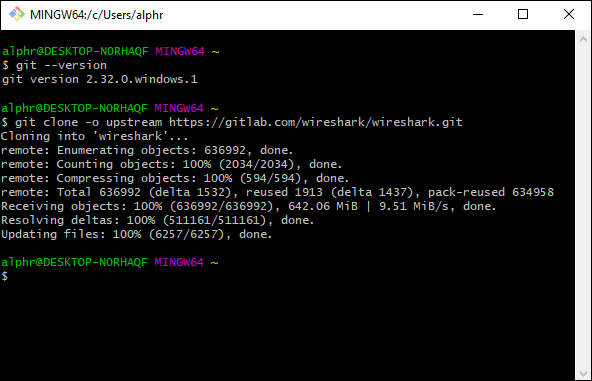
As the name suggests, the source of the packet is the place of origin. If you want to obtain the source code of a Wireshark repository, you can download it by using a Git client. However, the method requires you to have a GitLab account. It’s possible to do it without one, but it’s better to sign up just in case.
Once you’ve registered an account, follow these steps:
- Make sure Git is functional by using this command: “
$ git -–version.”
- Double-check if your email address and username are configured.
- Next, make a clone of the Workshark source. Use the “
$ git clone -o upstream git@gitlab.com:wireshark/wireshark.git” SSH URL to make the copy. - If you don’t have a GitLab account, try the HTTPS URL: “
$ git clone -o upstream https://gitlab.com/wireshark/wireshark.git.”
All the sources will be subsequently copied to your device. Keep in mind the cloning might take a while, especially if you have a sluggish network connection.
Destination
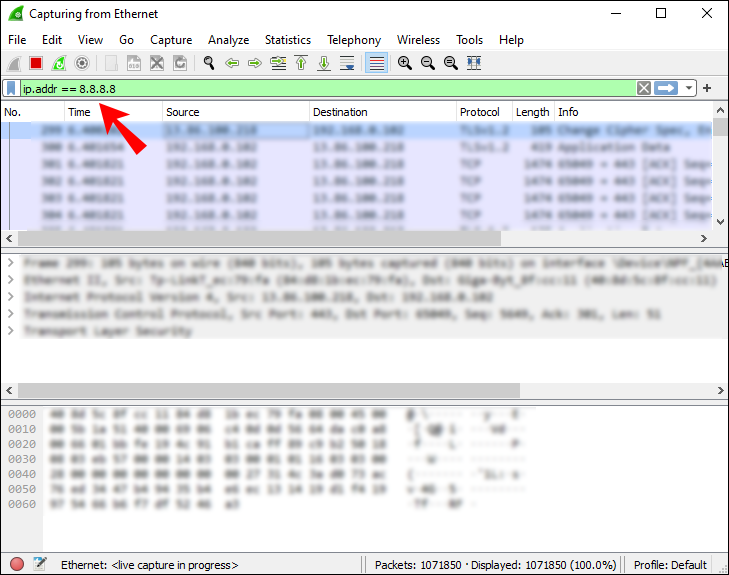
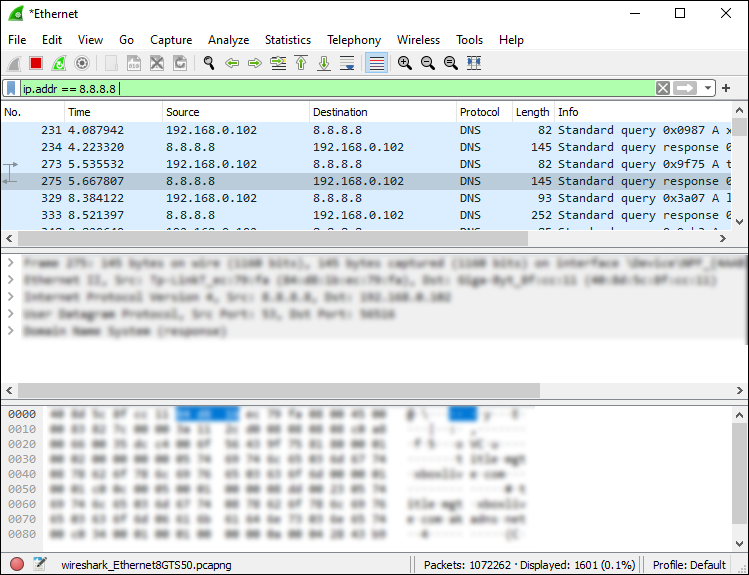
If you want to know the IP address of a particular packet’s destination, you can use the display filter to locate it. Here’s how:
- Enter “
ip.addr == 8.8.8.8” into the Wireshark “Filter Box.” Then, click “Enter.”
- The packet list pane will be reconfigured only to show the packet destination. Find the IP address you’re interested in by scrolling through the list.

- Once you’re done, select “Clear” from the toolbar to reconfigure the packet list pane.
Protocol
A protocol is a guideline that determines the data transmission between different devices that are connected to the same network. Each Wireshark packet contains a protocol, and you can bring it up by using the display filter. Here’s how:
- At the top of the Wireshark window, click on the “Filter” dialog box.
- Enter the name of the protocol you want to examine. Typically, protocol titles are written in lowercase letters.
- Click “Enter” or “Apply” to enable the display filter.
Length
The length of a Wireshark packet is determined by the number of bytes captured in that particular network snippet. That number usually corresponds with the number of raw data bytes listed at the bottom of the Wireshark window.
If you want to examine the distribution of lengths, open the “Packet Lengths” window. All the info is divided into the following columns:
- Packet lengths
- Count
- Average
- Min Val/Max Val
- Rate
- Percent
- Burst rate
- Burst start
Info
If there are any anomalies or similar items within a particular captured packet, Wireshark will note it. The information will then be displayed in the packet list pane for further examination. That way, you’ll have a clear picture of atypical network behavior, which will result in speedier reactions.
Additional FAQs
How can I filter the packet data?
Filtering is an efficient feature that allows you to look into the specifics of a particular data sequence. There are two types of Wireshark filters: capture and display. Capture filters are there to restrict the packet capture to fit specific demands. In other words, you can sift through different types of traffic by applying a capture filter. As the name suggests, display filters allow you to hone in on a particular element of the packet, from packet length to protocol.
Applying a filter is a pretty straightforward process. You can type the filter title in the dialog box at the top of the Wireshark window. In addition, the software will usually auto-complete the name of the filter.
Alternately, if you want to comb through the default Wireshark filters, do the following:
1. Open the “Analyze” tab in the toolbar at the top of the Wireshark window.
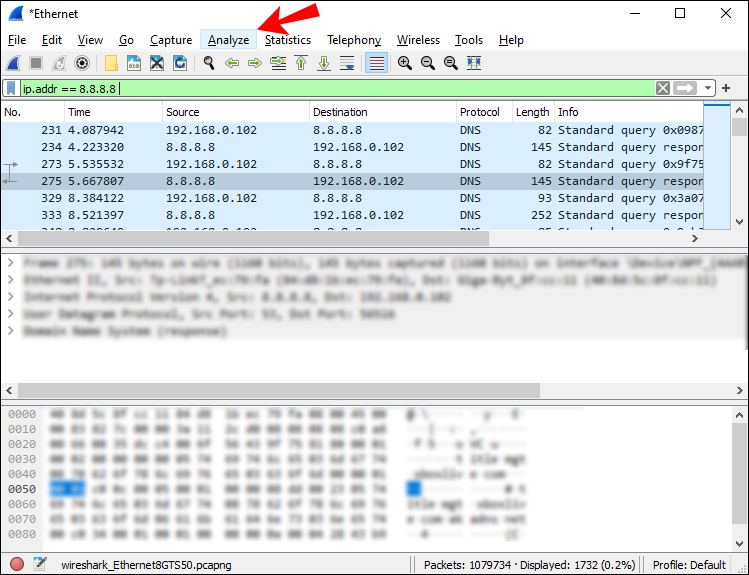
2. From the drop-down list, select “Display Filter.”
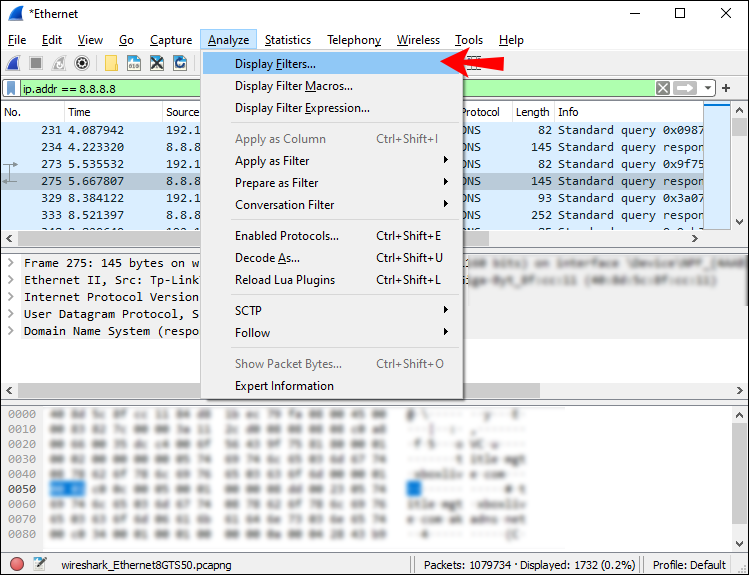
3. Browse through the list and click on the one you want to apply.
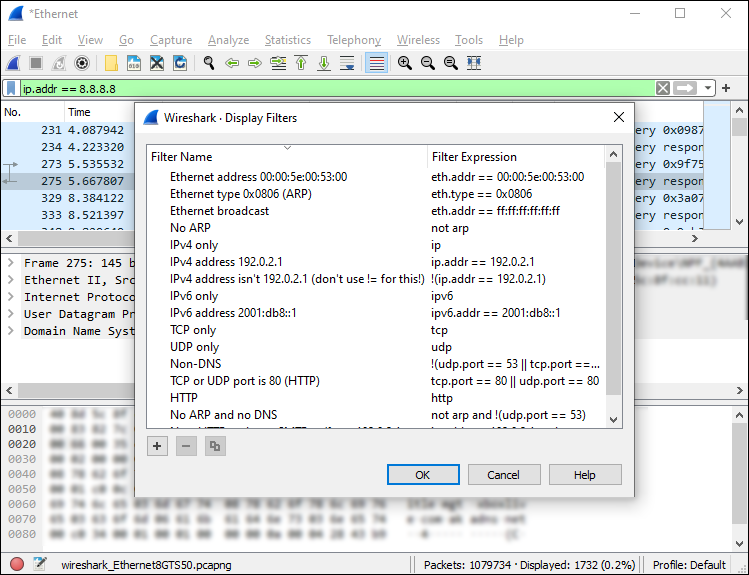
Finally, here are some common Wireshark filters that can come in handy:
• To only view the source and destination IP address, use: “ip.src==IP-address and ip.dst==IP-address”
• To only view SMTP traffic, type: “tcp.port eq 25”
• To capture all subnet traffic, apply: “net 192.168.0.0/24”
• To capture everything but the ARP and DNS traffic, use: “port not 53 and not arp”
How do I capture the packet data in Wireshark?
Once you’ve downloaded Wireshark to your device, you can start monitoring your network connection. To capture data packets for a comprehensive analysis, here’s what you need to do:
1. Launch Wireshark. You’ll see a list of available networks, so click on the one you want to examine. You can also apply a capture filter if you want to pinpoint the type of traffic.
2. If you want to inspect multiple networks, use the “shift + left-click” control.
3. Next, click on the far-left shark-fin icon on the toolbar above.
4. You can also start the capture by clicking on the “Capture” tab and selecting “Start” from the drop-down list.
5. Another way to do it is to use the “Control – E” keystroke.
As the software grabs the data, you’ll see it appear on the packet list pane in real-time.
Shark Byte
While Wireshark is a highly advanced network analyzer, it’s surprisingly easy to interpret. The packet list pane is extremely comprehensive and well-organized. All the information is distributed into seven different colors and marked with clear color codes.
Furthermore, the open-source software comes with a slew of easily applicable filters that facilitate the monitoring. By enabling a capture filter, you can pinpoint what kind of traffic you want Wireshark to analyze. And once the data is grabbed, you can apply several display filters for specified searches. All in all, it’s a highly efficient mechanism that’s not too difficult to master.
Do you use Wireshark for network analysis? What do you think of the filtrating function? Let us know in the comments below if there’s a useful packet analysis feature we skipped.
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.