As a free and open-source packet analyzer, Wireshark offers many convenient features. One of them is finding media access control (MAC) addresses, which can tell you more information about different packets on a network.
If you’re new to Wireshark and don’t know how to find MAC addresses, you’ve come to the right place. Here, we’ll tell you more about MAC addresses, explain why they’re useful, and provide steps for finding them.
What Is a MAC Address?
A MAC address is a unique identifier assigned to network devices like computers, switches, and routers. These addresses are usually assigned by the manufacturer and are represented as six groups of two hexadecimal digits.
What Is a MAC Address Used for in Wireshark?
The primary role of a MAC address is to mark the source and the destination of a packet. You can also use them to track a specific packet’s path through a network, monitor web traffic, identify malicious activity, and analyze network protocols.
Wireshark How to Find MAC Address
Finding the MAC address in Wireshark is relatively easy. Here, we’ll show you how to find a source MAC address and destination MAC address in Wireshark.
How to Find a Source MAC Address in Wireshark
A source MAC address is the address of the device sending the packet, and you can usually see it in the packet’s Ethernet header. With the source MAC address, you can track a packet’s path through the network and identify each packet’s source.
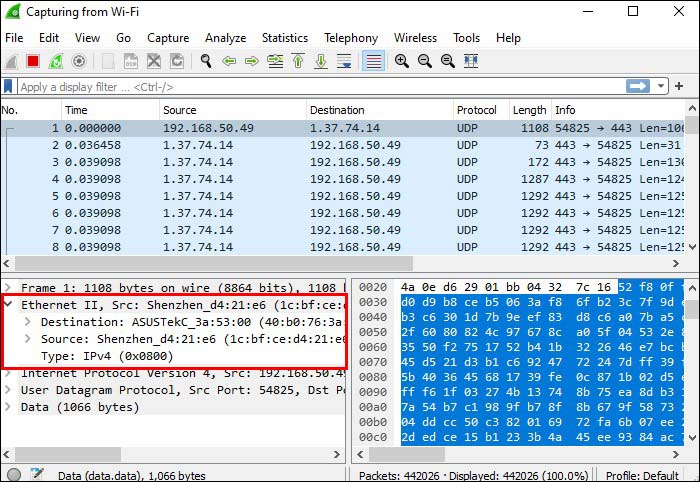
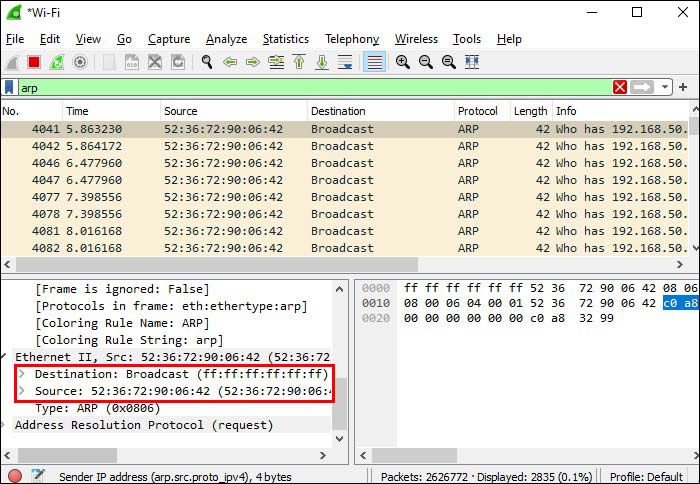
You can find the source MAC address of a packet in the Ethernet tab. Here’s how to get to it:
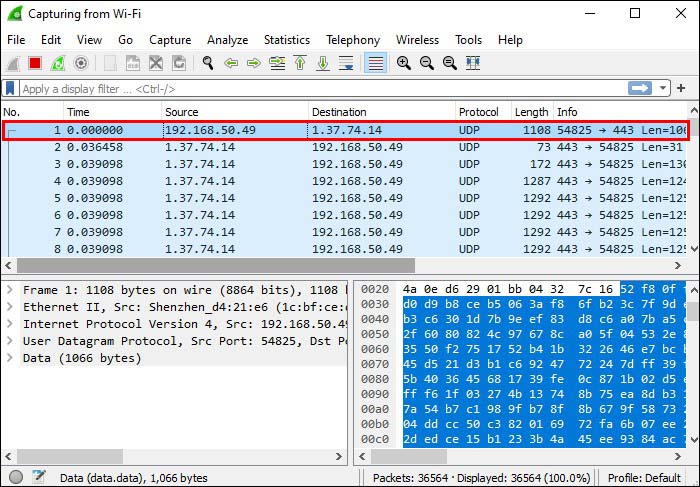
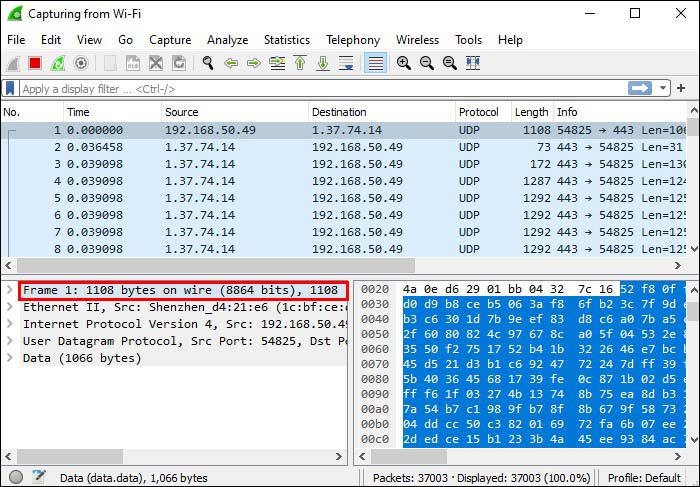
- Open Wireshark and capture packets.

- Select the packet you’re interested in and display its details.

- Select and expand “Frame” to get more information about the packet.

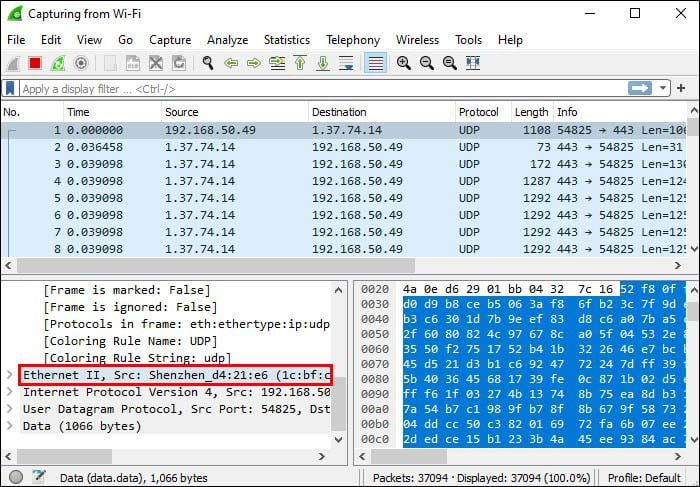
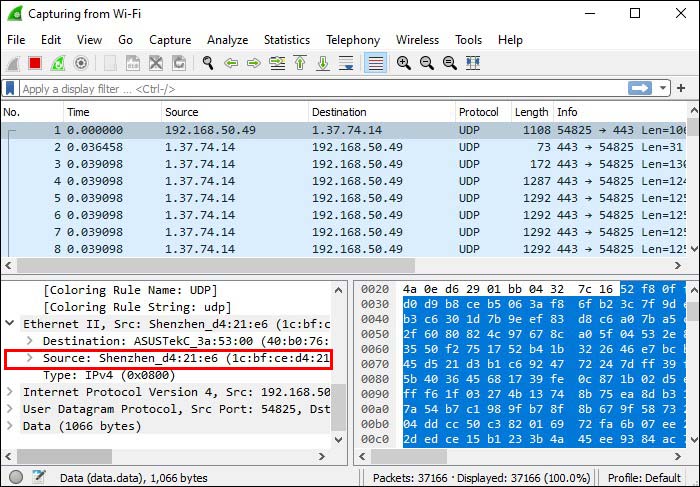
- Go to the “Ethernet” header to view Ethernet details.

- Select the “Source” field. Here, you’ll see the source MAC address.

How to Find a Destination MAC Address in Wireshark
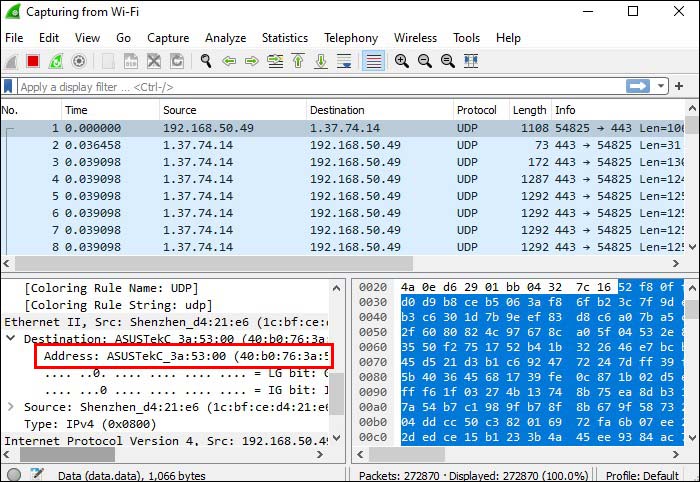
A destination MAC address represents the address of the device receiving a packet. Like the source address, the destination MAC address is located in the Ethernet header. Follow the steps below to find a destination MAC address in Wireshark:
- Open Wireshark and start capturing packets.

- Find the packet you want to analyze and observe its details in the detail pane.

- Choose “Frame” to get more data about it.

- Go to “Ethernet.” You’ll see “Source,” “Destination,” and “Type.”

- Select the “Destination” field and view the destination MAC address.

How to Confirm a MAC Address in Ethernet Traffic
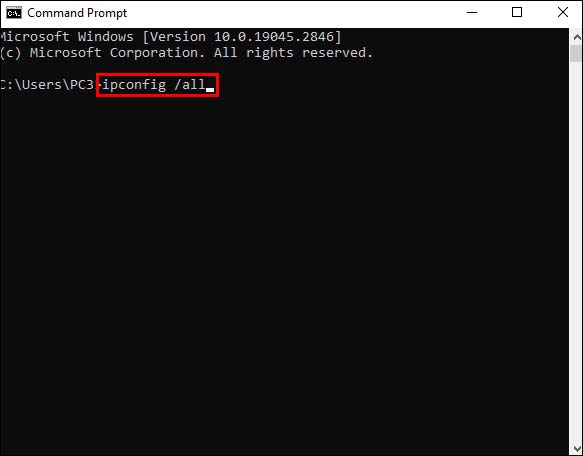
If you’re troubleshooting network issues or want to identify malicious traffic, you may want to check whether a particular packet is being sent from the right source and routed to the right destination. Follow the instructions below to confirm a MAC address in Ethernet traffic:
- Display your computer’s physical address by using ipconfig/ all or Getmac.

- View the Source and Destination fields in the traffic you’ve captured and compare your computer’s physical address to them. Use this data to check which frames were sent or received by your computer, depending on what you’re interested in.

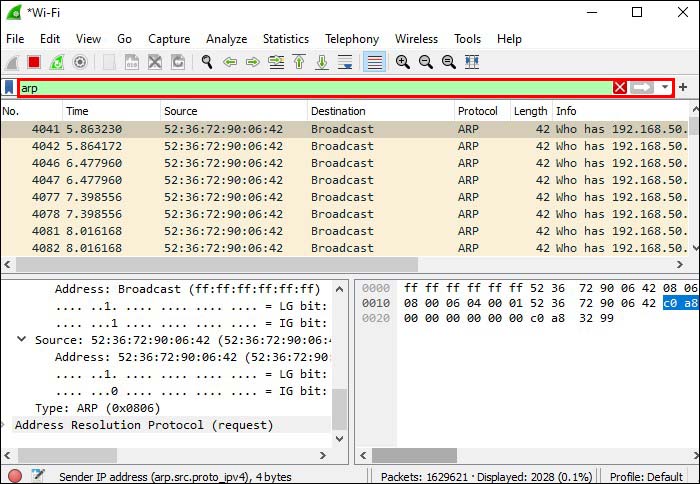
- Use arp-a to see the Address Resolution Protocol (ARP) cache.

- Find the default gateway’s IP address used in the command prompt and view its physical address. Check whether the gateway’s physical address matches some of the “Source” and “Destination” fields in the captured traffic.

- Complete the activity by closing Wireshark. If you want to discard captured traffic, press “Quit Without Saving.”

How to Filter a MAC Address in Wireshark
Wireshark allows you to use filters and go through large amounts of information quickly. This is especially useful if there’s an issue with a certain device. In Wireshark, you can filter by the source MAC address or the destination MAC address.
How to Filter by Source MAC Address in Wireshark
If you want to filter by source MAC address in Wireshark, here’s what you need to do:
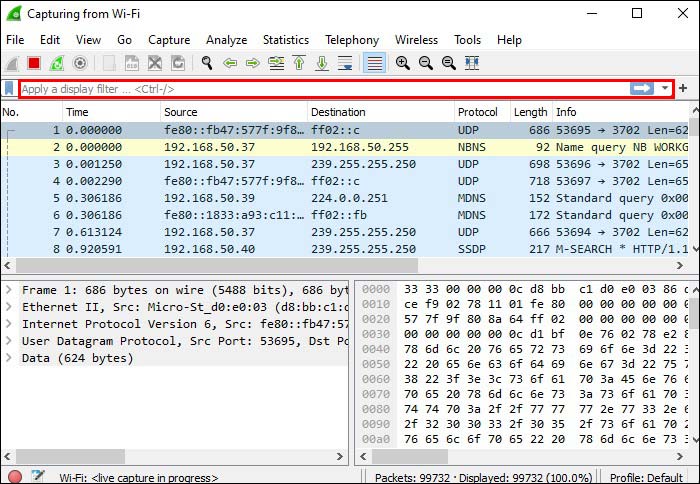
- Go to Wireshark and find the Filter field located at the top.

- Enter this syntax: “ether.src == macaddress”. Replace “macaddress” with the desired source address. Remember not to use quote marks when applying the filter.

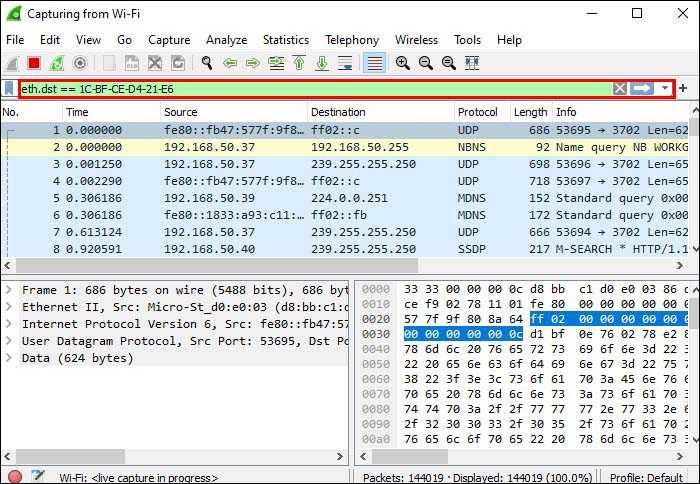
How to Filter by Destination MAC Address in Wireshark
Wireshark allows you to filter by destination MAC address. Here’s how to do it:
- Launch Wireshark and locate the Filter field at the top of the window.

- Enter this syntax: “ether.dst == macaddress”. Ensure to replace “macaddress” with the destination address and remember not to use quote marks when applying the filter.

Other Important Filters in Wireshark
Instead of wasting hours going through large amounts of information, Wireshark lets you take a shortcut with filters.
ip.addr == x.x.x.x
This is one of the most commonly used filters in Wireshark. With this filter, you display only captured packages containing the chosen IP address.
The filter is particularly convenient for those who want to focus on one kind of traffic.
You can filter by source or destination IP address.
If you want to filter by source IP address, use this syntax: “ip.src == x.x.x.x”. Replace “x.x.x.x” with the desired IP address and remove quote marks when entering the syntax into the field.
Those who want to filter by source IP address should enter this syntax into the Filter field: “ip.dst == x.x.x.x”. Use the desired IP address instead of “x.x.x.x” and remove quote marks.
If you want to filter multiple IP addresses, use this syntax: “ip.addr == x.x.x.x and ip.addr == y.y.y.y”.
ip.addr == x.x.x.x && ip.addr == x.x.x.x
If you want to identify and analyze data between two specific hosts or networks, this filter can be incredibly helpful. It will remove unnecessary data and display the desired results in only a few seconds.
http
If you want to analyze only HTTP traffic, enter “http” in the Filter box. Remember not to use quote marks when applying the filter.
dns
Wireshark lets you filter captured packets by DNS. All you have to do to view only DNS traffic is to enter “dns” in the Filter field.
If you want more specific results and display only DNS queries, use this syntax: “dns.flags.response == 0”. Ensure not to use quote marks when entering the filter.
If you want to filter DNS responses, use this syntax: “dns.flags.response == 1”.
frame contains traffic
This convenient filter lets you filter packets containing the word “traffic.” It’s particularly valuable for those who want to search for a specific user ID or string.
tcp.port == XXX
You can use this filter if you want to analyze the traffic that goes in or out of a specific port.
ip.addr >= x.x.x.x and ip.addr <= y.y.y.y
This Wireshark filter allows you to display only packets with a specific IP range. It reads as “filter IP addresses greater than or equal to x.x.x.x and less than or equal to y.y.y.y.” Replace “x.x.x.x” and “y.y.y.y” with the desired IP addresses. You can also use “&&” instead of “and.”
frame.time >= August 12, 2017 09:53:18 and frame.time <= August 12, 2017 17:53:18
If you want to analyze incoming traffic with a specific arrival time, you can use this filter to get the relevant information. Keep in mind that these are just example dates. You should replace them with the desired dates, depending on what you want to analyze.
!(filter syntax)
If you place an exclamation mark in front of any filter syntax, you will exclude it from the results. For example, if you type “!(ip.addr == 10.1.1.1),” you’ll see all packets that don’t contain this IP address. Keep in mind that you shouldn’t use quote marks when applying the filter.
How to Save Wireshark Filters
If you don’t use a particular filter in Wireshark often, you’ll likely forget about it in time. Trying to remember the correct syntax and wasting time searching for it online can be very frustrating. Fortunately, Wireshark can help you prevent such scenarios with two valuable options.
The first option is auto-completion, and it can be useful for those who remember the filter’s beginning. For example, you can type “tcp,” and Wireshark will display a list of filters beginning with that sequence.
The second option is bookmarking filters. This is an invaluable option for those who often use complex filters with long syntax. Here’s how to bookmark your filter:
- Open Wireshark and press the bookmark icon. You can find it on the left side of the Filter field.
- Select “Manage Display Filters.”
- Find the desired filter on the list and press the plus sign to add it.
The next time you need that filter, press the bookmark icon, and find your filter on the list.
FAQ
Can I run Wireshark on a public network?
If you’re wondering whether running Wireshark on a public network is legal, the answer is yes. But, that doesn’t mean you should run Wireshark on any network. Ensure to read the terms and conditions of the network you want to use. If the network prohibits the use of Wireshark and you still run it, you could be banned from the network or even sued.
Wireshark Doesn’t Bite
From troubleshooting networks to tracing connections and analyzing traffic, Wireshark has many uses. With this platform, you can find a specific MAC address in only a few clicks. Since the platform is free and available on multiple operating systems, millions of people worldwide enjoy its convenient options.
What do you use Wireshark for? What is your favorite option? Tell us in the comments section below.
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.