Cloud-based accounting software Xero is an excellent solution for managing the entire accounting process of your business. It is designed for business owners who don’t have accounting or bookkeeping qualifications and is relatively easy to use. Sometimes we click a little too quickly though, so if you’ve deleted a transaction that you’d like to see again, there is a way. It may be a little tricky to work out.
This article shows you how to find a deleted transaction and store it safely. We’ve included some helpful information on cybercrime and how to protect your business data.
How to Find a Deleted Transaction
Follow these steps to find and restore a deleted transaction.
- Sign in to Xero.
- From the “Accounting” menu, choose “Bank accounts.”

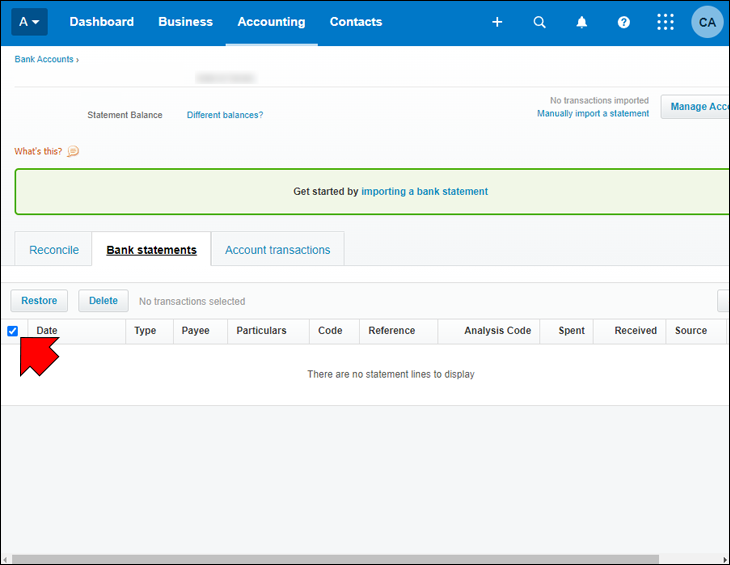
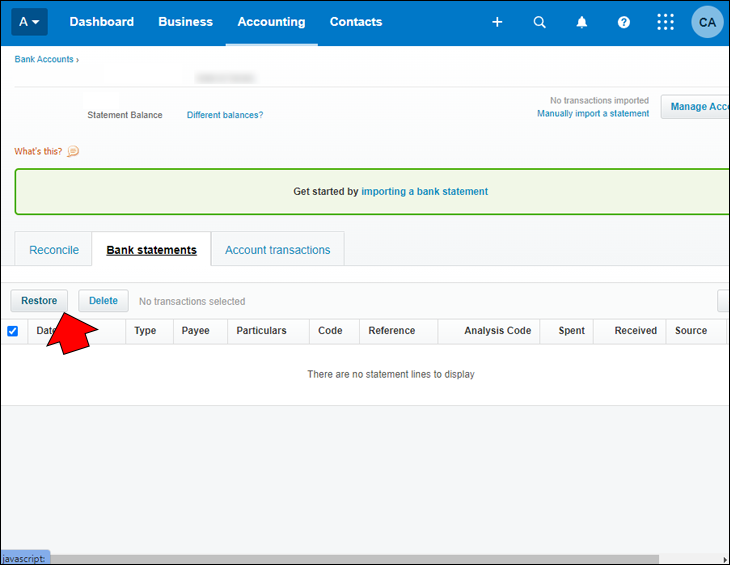
- Go to the bank account you wish to restore the bank statement line in, then choose “Manage Account” and “Bank Statements.”

- From the “Showing” option, choose “Statement lines.”

- Check the checkbox beside the statement line you want to restore.

- Click the “Restore” button.

Keep Your Restored Deleted Transactions Safe
Now that you’ve found your deleted transactions, you’ll want to store them safely. Cloud-based software offers several benefits for businesses, including flexibility, mobility, and collaboration support. Unfortunately, cybercriminals’ dreams of easy access to data have come true.
Many small business owners may feel they fall under the radar regarding cybercrime. However, small businesses get hacked more than larger businesses. Before learning how to protect your data from the bad guys, understand why smaller companies are targeted more.
Every Business Has Resources Worth Hacking
All businesses, including a one-person shop, will have data that is valuable to a cybercriminal. For example, email addresses, tax ID numbers, credit card numbers, and even Apple Music accounts. Cybercriminals can earn money from this information on the dark web.
Small Companies Typically Spend Less on Cybersecurity
Many small business owners find expenditure prioritizing like a juggling act. Although many leaders know the importance of cybersecurity for their business, it may not be a priority.
Cybercriminals are well aware of this. That’s why they focus on smaller businesses, as they know it will be less challenging to receive a payout than they’d get from the effort required to hack more prominent companies.
Small Business Are Often Unprotected From Ransomware
During the last decade, ransomware has been one of the fastest-growing forms of cyberattack. The number of victims who have paid the ransom demanded in order to get their data back has also increased as online criminals use more sophisticated ways to trick people.
Due to its rising success, many hackers are venturing down the ransomware route. Criminals just starting will first target a small business for easier intrusion.
Hackers Can Gain Access to Larger Companies Through Smaller Ones
If a cybercriminal breaks the network of a smaller business, they often use this success for entry into a larger company. Many small enterprises deliver services to larger corporations, such as website management, accounts, digital marketing, etc. Retailers are often electronically connected to specific client systems. This setup can facilitate multi-company breaches.
Staff May Not Be Well-Trained in Cyber Awareness
Cyber awareness training can be another task challenging to prioritize in a small company with busy employees wearing many hats. However, human error leaves businesses more susceptible to cyber risk. For cyberattacks to be successful, they mostly need assistance from users. If staff isn’t trained on the telltale signs of a phishing email, for instance, they could play a part in a successful attack. Fruitful phishing attempts cause nearly all data breaches. Teaching employees how to spot these ploys can considerably tighten cybersecurity.
How to Protect Your Business From Cybercrime
Cloud-based tools like Xero are handy to support you in running your business efficiently and cost-effectively. Unfortunately, online criminals continuously look for ways to gain access to data due to increased reliance on the cloud.
You won’t have time to keep track of all the constantly evolving cyber threats. However, you should be sufficiently protected if you focus on these three areas of concern.
1. Look Out for Phonies
Online criminals are skilled at impersonating almost anyone and will do whatever is necessary to gain your trust and trick you into something risky. Here are the types of imposters you and your teams should be aware of and how to protect yourselves and your company against cyber threats.
Phishing and Phone Scams

Phishing is sending messages that mimic legitimate communication in a fraudulent attempt to trick people into revealing their personal information.
- Phishing attempts can occur via email, text messages, or phone calls pretending to be customer support or other employees of a company.
- Attachments and links included in phishing messages are used to infect devices and steal account credentials.
- Cybercriminals can also infiltrate inboxes with weak passwords and even modify PDF invoices.
Consider these methods to protect your business:
- Train your staff to recognize the telltale signs of phishing emails to reduce the risk of clicked links.
- Have anti-malware software installed on all company devices.
- Use strong passwords and multifactor authentication throughout the company.
2. Defend Against Attackers

Using unsecured technology is an attractive target for online criminals. The company’s data and accounts can be at risk from a cybercrime attack when criminals seek security vulnerabilities in your technology. Trouble can occur through insufficient security maintenance or as a consequence of a previous incident like phishing.
Understanding the attack methods used and how to block vulnerabilities is the key to prevention. Some attacks are hard to detect and may resemble a legitimate program or file. It may discreetly monitor your activity.
- Malware – Malware is intrusive software intended to damage and destroy computers and computer systems. It can leak private information, prevent access to information, and gain unauthorized access to systems or data, among other forms of disruption.
- Ransomware – This is a severe variant of malware that is growing in popularity. It can take on several forms and have many impacts and symptoms.
You can protect your business against these types of attacks by:
- Running anti-virus software and keeping the software on your devices up-to-date.
- Protecting against account hijacking by using strong and unique passwords on devices and company accounts and ensuring everyone avoids reusing passwords.
- Using a password manager that can help create strong passwords for your accounts and sync them across several devices for quicker sign-ins.
3. Regularly Check Your Blind Spots

As your business grows, the size and complexity of the data you hold increases. It may become overwhelming to manage and challenging to protect. The risks and obligations associated with business data may be discovered only after it’s too late. You must be aware of your business’s blind spots in conjunction with the phonies and attackers.
In addition to securing sensitive and confidential company data against online criminal threats—such as your restored deleted transactions in Xero—there is another type of data that you’re obligated to protect that often gets overlooked.
Personal Data

- Personal data can identify someone physically and logistically, and may be harmful to them if exposed. This includes data related to you, your customers, suppliers, employees, or family members.
- Be mindful of payment information such as credit card numbers, contact details, ID numbers, bank account numbers, social security numbers, passport and driver’s license numbers, etc.
- Although this data is helpful for your business operations, it comes with ethical, legal, and contractual requirements around its use.
Global Privacy Laws

There is international legislation created to hold businesses accountable and to protect individuals—for example, GDPR. Your company must comply with privacy laws in your business regions, and failing to comply could result in serious legal action.
Insider Threats

- Misuse – Risks to your business information may come from inside your business, either deliberately or accidentally.
- Mishandling – Staff may unknowingly expose sensitive data through sharing or insecure storage.
- Malicious intent – An unhappy employee may use their ability to access certain information and use it for profit or revenge.
Here’s how to protect yourself.
- Review the personal information your company holds and ensure it is stored securely and in line with best practices.
- Train your employees on the secure way to handle, store, and share personal information.
- Get familiar with the privacy laws in the countries you operate in, as laws may differ.
- Limit access to personal information. Only allow access to team members who need it to perform their roles.
- Ensure shared logins aren’t being used; this helps develop an audit trail should you need to investigate an incident.
FAQs
How long does it take to learn Xero?
The Xero certification for accountants and bookkeepers can be completed through an online course, live webinar, or a fast-track Xero advisor. It takes around 6-8 hours to complete the Xero certification.
Can I learn Xero by myself?
Xero isn’t difficult to use. However, if you’re unfamiliar with online accounting software and are learning how to use it independently, there can be quite a learning curve.
Deleted Transaction Restored
Xero accounting software offers a well-organized interface, but for some, learning how to use it can be challenging. Fortunately, it allows you quick access to deleted transactions in the event something is accidentally deleted. Deleted transactions will display in the Bank Statements area, where you can select the transaction and choose Restore.
Were you able to find and restore the deleted transaction you wanted? Did you learn any new ways to protect your data from cybercriminals from this article? Share your experience with us in the comments section below.
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.