Security-wise, the internet can be a wild place sometimes. With more than half of the world’s population online, viruses, phishing, and malware attacks are ever-present. Knowing the difference between a harmless link and a villainous attempt is primordial.
But how do you check a link for a virus? This is the question we will answer in today’s guide. Keep reading to discover different tips and techniques that tell you whether the links you are being served with every day are safe.
How to Check a Link for a Virus?
If you’ve been on the internet for a while, there’s a high probability someone tried to trick you into getting your personal information. Whether you’re a Mac, Windows, Android, or iPhone user, it makes no difference. With the lack of awareness, everyone can become a victim of malicious attacks.
Fortunately, there are things you can do to protect your data and device’s safety. Below, we’ll cover some of the most common techniques you can apply to verify links for viruses.
Real-Time or Active Scanning
What is real-time and active scanning? Real-time scanning is a persistent, ongoing scan that scans files for security risks every time they are downloaded or opened. Users can only proceed to the file if it shows no vulnerability risks.
Active scans send test traffic into the network and query individual endpoints. They collect basic information such as IP addresses, device names, and more. Typically, users cannot find the information contained in active scans in usual data traffic.
Both real-time and active scans are the backbone of internet security. There are a few excellent software solutions called antiviruses that offer robust protection:
Norton
Norton is one of the most powerful, feature-packed antivirus software currently on the market. It has a special product called Norton 360, specifically designed for internet security. Some of its features include anti-spyware, antimalware, anti-phishing, antivirus, and ransomware protection.
Kaspersky

Along with Norton, Kaspersky is another cybersecurity giant. It also has a dedicated internet security suite fully equipped to combat malware, ransomware, spyware, phishing attacks, and much more. With Kaspersky’s Internet Security Advanced Suite, you also get payment protection to ensure your banking information is safe.
Other popular antiviruses with internet security tools include McAfee, AVG Antivirus, Bitdefender, and ESET Smart Security Program.
If you’re looking for a long-term solution to verify links for viruses, antivirus software is the way to go. Note that most antivirus software offers the best protection in the paid versions. However, they are worth the investment for everyone looking to add a layer of security to their daily browsing experience.
Link Scanners
If you don’t use antivirus protection on your device, simply visiting a malicious website can be enough to infect your system. Maybe you’ve received a suspicious link from a phisher through your email or a comment on your social media page. Opening it may lead you to phishing websites that are particularly built to steal users’ personal information.
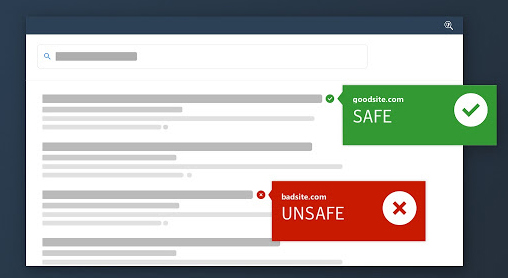
To verify links before opening and prevent malware attacks, you can use link scanners. These tools identify malicious links by checking them against their own databases. A drawback, however, is that these scanners can’t flag new fraudulent URLs since their databases may not have daily updates.
Here are some places where you can scan suspicious links before opening them:
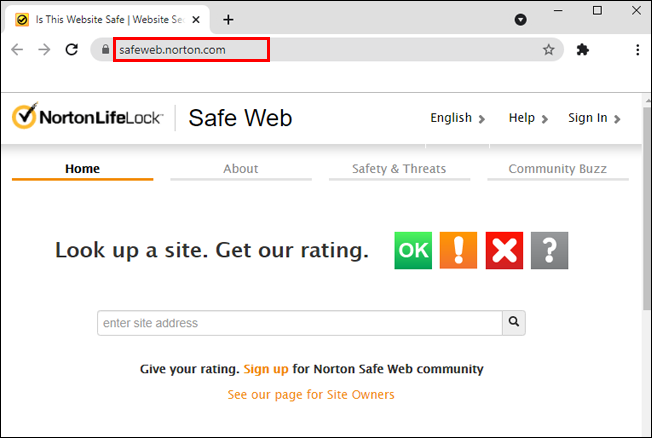
- Norton Safe Web lets you look up a site for safety and security issues. If threats are detected, you’ll get a report on that site’s computer.

- Google Transparency Report checks billions of URLs daily in search of harmful websites. Simply head over to the website and paste the link to see whether the website is dangerous to visit at the moment.

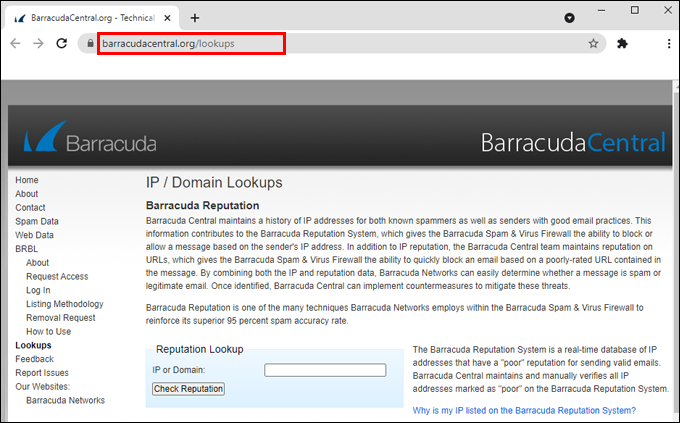
- Barracuda Central keeps a history of IP addresses known for spam or the ones with a poor reputation. The program can block messages from these sources, keeping your mailbox safe from various kinds of malicious threats.

- Is It Hacked is a simple to use, free online resource that checks whether URLs are suspicious by looking for blacklist checks, spammy-looking links, status codes, and so on.

- Trend Micro Site Safety Center verifies links based on the website age, historical locations, and changes, as well as indications of fraudulent activities found through malware behavior analysis.

- Bright Cloud Threat Intelligence lets you view threats, content, and reputation analysis of URLs.

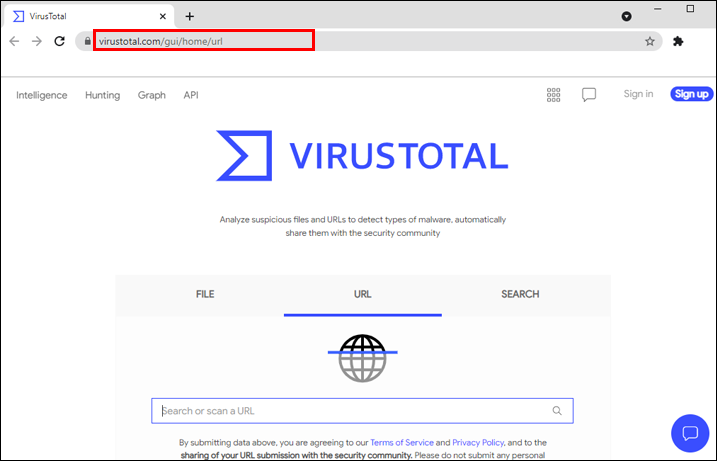
- Virustotal is a great platform that lets you analyze suspicious files and URLs and detect various malware types. Simply click on the “URL” section and follow the instructions.

All you have to do to scan links on these websites is copy its URL into the URL box featured on-site and click on “Check Reputation,” “Look Up,” “Check Now,” and similar buttons next to the box.
Decode Coded URLs
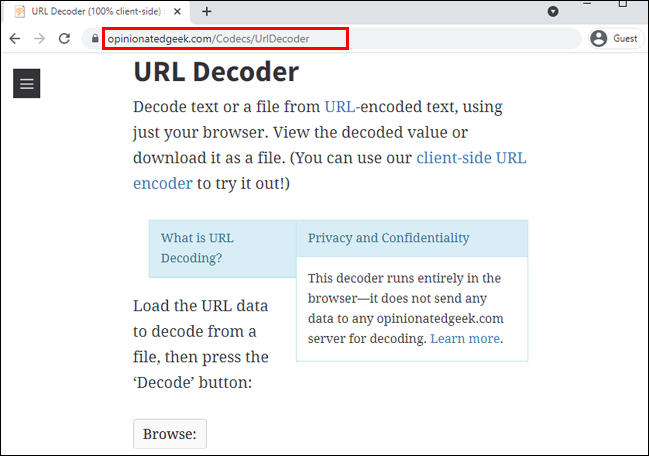
Some hackers may use URL encoding to mask destinations, commands, and other clues from the link to remain invisible to the user. By using percentage-based URL encodings, their phishing campaign can also remain undetected by email gateways.
Fortunately, you can use URL decoding tools to reveal the exact link destination.
- URL Decoder helps encode or decode data by simply entering the URL in the text box and clicking on the “Decode” button.

- Opinionated Geek has a free service that lets you paste and decode URLs directly in your browser. Just paste the URL and click on “Decode.”

- URL Decode Online is another free tool that lets you effortlessly convert encoded URLs into a regular URL string.

Be Wary of Unsolicited Emails
Email is one of the most straightforward channels for hackers to share malicious information. Your email provider most likely has a separate “Spam” folder for suspicious, unsolicited emails. Clicking on the links in your Spam folder can redirect you to the phishing website or ones that install malware on your device.
To protect your email inbox from these attacks, follow these simple steps:
- Don’t post your email address publicly. Hide the address whenever possible, as there could be lurking eyes everywhere.
- Think twice before clicking. If you notice an email that offers cheap prescription drugs, promises to give you money, or has status packages from shipping companies and similar, there’s a good chance it’s spam. Don’t download or click on any content coming from a service or an email address you find suspicious.
- Don’t reply to spam. Spammers send bulk emails to millions of emails. If you answer a spam message, you’ll let them know the address is active. This will increase the chance of you receiving even more spam in the future.
- Use antivirus or link scanner tools. Use the services we’ve provided above to check any links to questionable sources in your mailbox.
Inspect Short Links Using Link Expansion
There are two types of URLs circulating the web:
- Standard-length ones that start with “www” are followed by the site name and end with “.com” or other domain endings.
- Shortened URLs, convenient for sharing on social media, where you can’t see where the link is leading by looking at it.
Due to their shortened visibility, short URLs are convenient for phishers and malware hackers who want to steal user identity, get access to sensitive data, or perform other harmful actions.
Fortunately, you can use some convenient online tools to expand and verify the link or expand it to see its original counterparts.
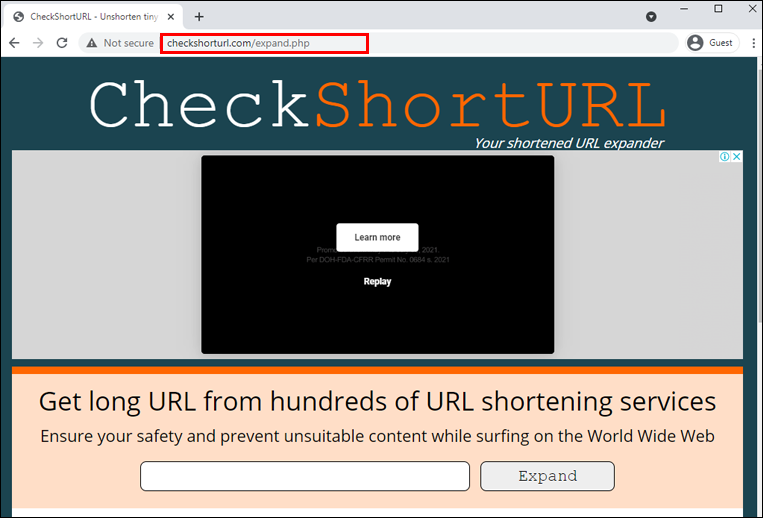
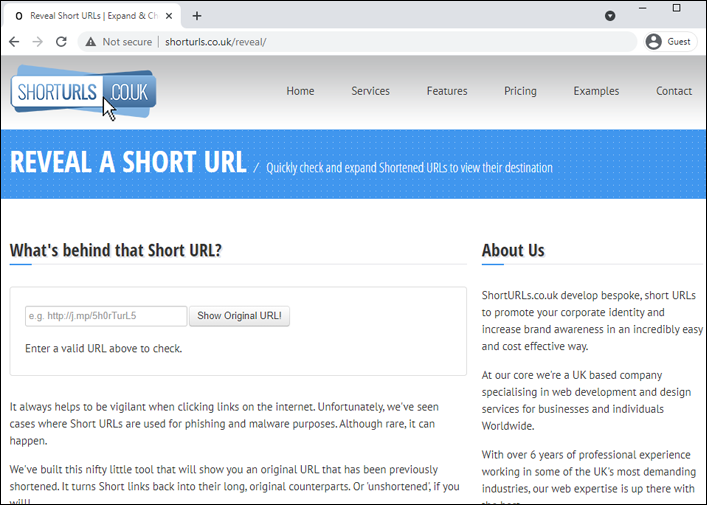
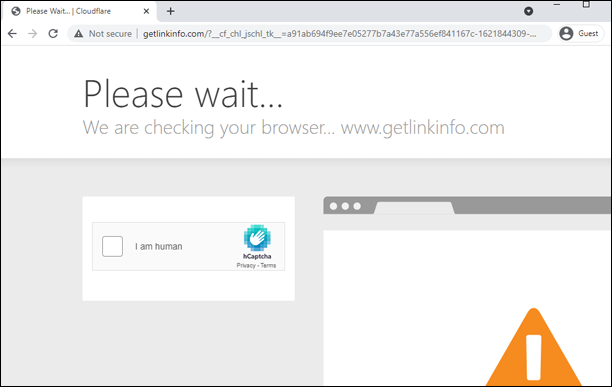
- Check Short URL checks shortened URLs to determine their actual source, ultimately preventing you click on malicious links.

- Short URLs let you quickly check and expand shortened links and lets you see their destination.

- Get Link Info is an informative website that tells you the main title of the page, the full URL address, and all external links on the page you’re visiting.

Additional FAQs
Here is some more answers to help you browse the web safely.
How to Check if a File Has a Virus?
Antivirus and antimalware programs are built especially for scanning files against viruses. If a file you intend on downloading is infected with a virus, your antivirus should be able to recognize it.
You can also check by right-clicking on the file and studying its properties. If a legitimate company is stated under “Publisher,” then the file is most likely safe.
Some online websites, such as VirusTotal we already mentioned today, let you scan files for potential threats. Just click on the “File” section, upload a file from your computer, and you’re good to go.
How to Tell if a Link Is Suspicious?
There are several ways to tell if a link you’ve stumbled upon is suspicious:
· Hover over the link. The attackers often lure users with links that appear like a legitimate website, for example, www.youtube.com, but then redirect them to an entirely different place. You can simply check a suspicious link by hovering over it with your mouse. There should be a small box telling you where the link will take you.
· It’s asking for private information. If a specific financial institution sends you an email and provides a link to enter your personal information, always double-check or call the company to verify link validity.
· Blacklisted domains. You can check for links with blacklisted domains on the websites we provided in the “Link Scanning” section.
· URL with spammy phrases. If you see words such as “online dating,” “please help,” “extra income,” “donate,” and such, feel free to mark those as spam.
Safety and Security First
As the number of URLs and data shared online increases, so do various phishing and malware attacks. To keep your personal information and data secure, you should always verify links before clicking on them. Fortunately, there are many methods for doing so, and we covered some of the safest ones today.
If you browse the internet and deal with URLs daily, you may want to consider installing antivirus software. Alternatively, you can always run quick link scans to check for URL vulnerabilities.
Which method for checking a link for viruses do you find the most convenient? Do you perform regular security checks on your computer? Share your experiences in the comments section below.
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.