Information security might seem like a modern concern, but as long as there has been civilisation, there has been a need to stop sensitive information getting into the wrong hands. Cryptography has always played a crucial role here, as those with the information encrypt it to control who can read it, while those who want the information find new ways to break the code.
The beginnings of cryptography
Cryptography dates back to ancient times. As far back as 2,000BC the Egyptians were using complex and cryptic systems of hieroglyphics to decorate tombs, not so much in order to conceal the meaning as to make their dead nobles more enigmatic. There’s also evidence that the Mesopotamians encrypted cuneiform text to hide information, while the Hebrews of the 5th century BC used simple ciphers, substituting the last letter of the alphabet for the first, the penultimate for the second, and all the way down the line. The Spartans of the same era came up with an ingenuous system, writing messages on thin sheets of papyrus, wrapped around a baton or “scytale”. The sheet would be unwrapped, encrypting the message, and it could only be decrypted when wrapped once more around a scytale of the same diameter. This enabled the Spartans to send and receive secret military plans in confidence.
With time, methods grew more sophisticated. In the second century BC, the Greek scholar Polybius laid out the alphabet in a grid of five by five squares, then prescribed using torches or hand signals to relay encrypted messages, coordinate by coordinate. Julius Caesar had his own cipher, shifting each letter in a message two places further down the alphabet.
Making codes was one thing, but breaking them was another. The great pioneer of cryptoanalaysis – the study and breaking of encryption – was the Arab polymath al-Kindi, who in the 9th century AD applied scientific methods, using the frequency with which letters are used in a language as a means of breaking down the cipher. His work informed that of Ibn al-Durayhim who, in the 13th century, gave detailed descriptions of new systems that involved more complex letter-for-letter substitutions – systems that would be much harder to break.
Cryptography in power
Italy in the 15th century was one of history’s great hotbeds of intrigue, as different Italian city states vied for power. The courts of Rome, Florence and Milan made extensive use of cryptography, while Venice had its own secretaries trained to encrypt and decrypt messages passing to and from the Doge. Across Europe, methods became more sophisticated. A Genoa-born Florentine, Leon Battista Alberti, developed a system of polyalphabetic substatiation using two copper discs, each one bearing the alphabet. In 1518, the German monk Trimethius introduced a complex cryptographic table, the Tabula Recta, which was expanded by an Italian cryptologist, Giovan Battista Bellaso, and subsequently a French diplomat, Balise de Vigenere. These tables defined cryptography for the next 400 years.
By the 17th century, cryptography had become of national importance. In 1628, Henri, Prince of Conde laid siege to the Hugenot city of Realmont in Southern France. A coded message from the besieged city was intercepted and deciphered by a local mathematician, Antoine Rossignol, revealing the Hugenots’ lack of ammunition. The subsequent surrender caught the attention of Cardinal Richelieu, who brought Rossignol into the service of Louis XIV. There, Rossignol and this son developed a new code known as the Grand Cipher and ran a code breaking agency, the Cabinet Noir. Within a few decades, the so-called Black Chamber was a must-have for any European court.
Cryptography at war
Cryptography was to play a crucial part in the Napoleonic Wars of 1803 to 1815. Having been embarrassed by the number of communications being intercepted by British forces, Napoleon asked the French army to create a new, unbreakable code, known as the Army of Portugal Code. In active use by the spring of 1811, the code was broken in November by an English officer, Major George Scovell – in just two days, armed only with a guide to cryptography and a handful of captured messages. The French responded in early 1812 with a new code, the Great Paris Cipher, with over 1,400 numbers that could substitute for words or parts of words in millions of permutations. Scovell’s work had given Wellington a tactical advantage. Now, the major was tasked with breaking the new code.
Within a year, he had done so. The cypher might have seemed unbreakable, but the French officers using it became complacent, encrypting only portions of the message and leaving other parts in plain text. This gave Scovell enough to deduce what some of the encrypted words were, and the more messages Scovell gathered, the more of the cipher he broke. By July, enough of the cipher was broken for the British to decrypt a message from the French commander in Spain regarding reinforcements, enabling Wellington to pre-empt their arrival and seize victory at Salamanca. After that, Wellington could plan the Iberian campaign with almost complete intelligence of French plans, enabling him to drive Napoleon’s armies across northern Spain towards defeat.
Cryptography in the Machine Age
The development of the telegraph during the 1830s revolutionised communications, both in the commercial and military spheres. With the invention of radio in 1894, real-time wireless communications became a reality. Yet while telegraph and radio communications became crucial for diplomacy, espionage and warfare, encryption and decryption were still carried out by hand, or using simple, rotor-based devices like the 1785 Jefferson Wheel. A system using 26 wheels threaded on an iron spindle, which could be reassembled daily in any order, this remained the mainstay of US encryption for the best part of 150 years.
With the end of the First World War, however, cryptography entered the machine age. In 1915, two Dutch naval officers created a mechanised rotor-based system, and by 1919 similar systems had been demonstrated in the US by Huge Hebern, in Holland by Hugo Koch and in Germany by Arthur Scherbius. Scherbius’s machine, demonstrated in Bern in 1923, was adopted by the German Navy in 1926 and by the German Army in 1928. Scherbius called it Enigma.
Cryptography had been crucial during First World War, where the work of the British Admiralty’s code-breaking office, Room 40, lead directly to the battles of Jutland and Dogger Bank and, through the decryption of a German diplomat’s telegram, the United States’ entry into war. During the Second World War, however, it became absolutely critical. Isolated from Nazi-occupied Europe, Britain was dependent on Atlantic convoys under constant threat from German U-Boats. The U-Boats worked individually but, on finding a convoy, made contact with other U-Boats, using radio to set-up highly coordinated attacks. These messages were enciphered by the German Navy’s Enigma machines, so breaking Enigma became a matter of survival.
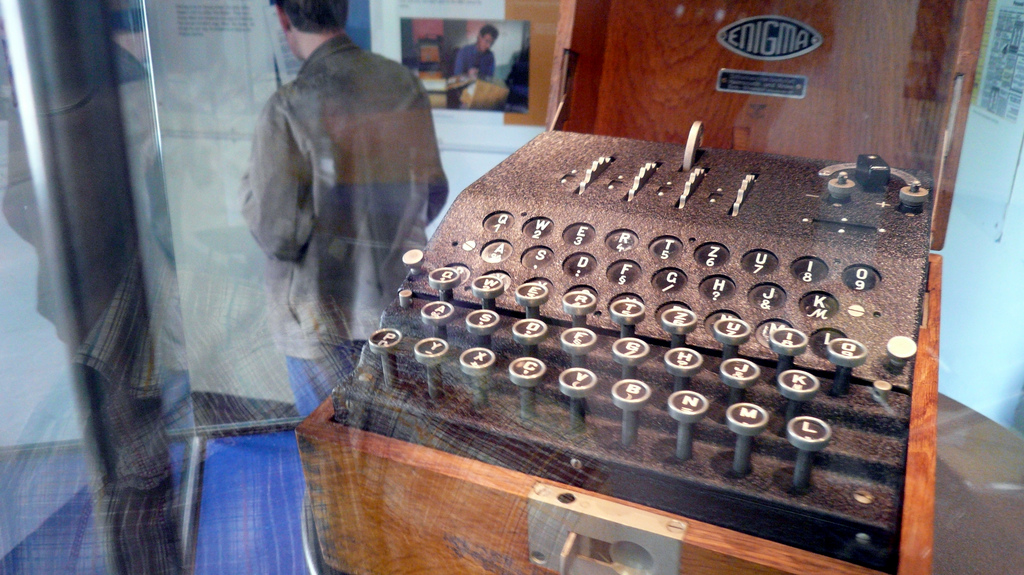
The German Army’s Enigma system had actually been cracked in 1938 by Mario Rejewski in Poland, and the Polish had passed on their expertise and pioneering Bomba decoding machines shortly before the German invasion. However, where the army’s Enigma machines used three rotors from a set of five to encrypt and decrypt messages for the day, the Navy’s used three of eight. What’s more, the Navy had more complex procedures to set up message keys, detailing the initial rotor positions at the beginning of encryption.
At Bletchley Park in England, Alan Turing and Gordon Weichman did substantial work on the Polish Bomba and created a new version: a code breaking machine that could work out the set of rotors in use for a day and their positions from a crib – a section of plain text believed to correspond to the intercepted ciphertext. Meanwhile, Turing, Max Newman and Tommy Flowers created Colossus – the world’s first programmable electronic digital computer – and so broke the complex cyphers used by the German High Command. Together, Turing’s Bombe and Colossus helped turn the tide of the war, shortening it by many months and saving many thousands of lives.
Cryptography meets the Computer Age
The arrival of the computer and the use of computers to store sensitive information created new challenges for cryptography. Computing enabled organisations to store, secure and analyse data more efficiently, but it also empowered new approaches to breaking code. In 1949, Claude Shannon’s paper, Communication Theory of Secrecy Systems, established a basic theory for maths-based cryptography in a computer age. In 1976, Whitfield Diffie and Marti Hellman introduced the concepts of asymmetric key encryption and the public key. This idea was revolutionary: a system that used not one key to encrypt and decrypt, but two pairs of mathematically-related keys, each of which could decrypt messages encrypted by the other. Their work informed the RSA cryptosystem that sits at the heart of most cryptography systems to this day.
Governments demanded new levels of security. In 1979, IBM, with input from the NSA, developed the Data Encryption Standard (DES) – a cutting-edge 56-bit encryption standard that was so advanced that even supercomputers couldn’t crack it. This remained the US government standard for almost 20 years until it was replaced in 1997 by the modern Advanced Encryption Standard (AES). In its weakest 128-bit form, AES would have taken computers of the time two to the power of 55 years to crack.
Today, we take these things for granted. Businesses purchasing new HP laptops and desktop PCs can protect their data with Windows 10 Professional’s built-in Bitlocker encryption, which uses AES in conjunction with a key embedded in the system’s Trusted Platform Module chip to lock-down the data on the hard disk. That’s security the governments of fifty years ago couldn’t have dreamed of. Meanwhile, HP’s Atalia Network Security Processors give some of the world’s largest corporations peace of mind that their data is secure – a must when handling sensitive financial information. While the continual growth of computing power makes today’s security threats ever more formidable, our encryption technologies remain strong. We’ve come a long way from hieroglyphics and the Spartan scytale, but we’re still keeping information safe.
Main image by Adam Foster. Enigma machine image by Cory Doctorow. All images used under Creative Commons licenses – thank you, photographers!
Disclaimer: Some pages on this site may include an affiliate link. This does not effect our editorial in any way.